Technical notes for Cisco Certification Exam 200-105 ICND2
This article contains the Technical notes for Cisco Certification Exam 200-105 ICND2, that I took to pass this exam, the final exam to obtain the CCNA
If you are in the world of IT, and have a minimum of interaction with networking devices, holding a CCNA certification (and obviously its knowledge) is critically important, not just for the professional relevance in the market that a Cisco certification has, but mostly for all the training, troubleshooting techniques and experience that you'll learn during the certification learning process. The exams topics for the ICND2 are here:
and just so you know the basis, a switch forward Ethernet frames, while a router forward packets! Ehterchannel, port-channel and channel-group are all the same thing. in STP bridge-ID is actually switch ID
A description of the exam itself can be found here: http://www.cisco.com/c/en/us/training-events/training-certifications/exams/current-list/200-105-icnd2.html
I passed the Cisco 200-105 ICND2 exam on 6th May 2019 at the Middlesex Academy of Business & Management, in Brick Lane, London, with a 85% score, yah!
- VLAN Trunking (802.1Q)
- VLANS
- VLAN Trunking Protocol (VTP)
- Spanning Tree Protocol (STP 802.1D)
- Rapid STP (802.1w)
- per-VLAN Spanning Tree (PVST)
- EtherChannel (known as port channel)
- PortFast and BDPU Guard
- Troubleshooting spanning tree
- AAA IEEE 802.1x
- DHCP Snooping
- Switch Stacking and Chassis Aggregation
- IPv6 Routing
- OSPF (administrative distance 110)
- Useful links about OSPF
- IPv6 with OSPF
- The Maximum Transmission Unit (MTU) issue
- EIGRP (administrative distance 90)
- Useful links about EIGRP
- IPv6 with EIGRP
- BGP (Border Gateway Protocol)
- Useful links about BGP
- Implementing PPP
- MPLS and WAN Services
- GRE Tunnels and DMVPN (Dynamic Multipoint VPN)
- PPP over Ethernet (PPPoE)
- ACLs
- ACL in IPv6
- Quality of Service (QoS)
- Classification and Marking
- Congestion Management (Queuing)
- Shaping and Policing
- Congestion Avoidance
- Routing
- Hot Standby Router Protocol (HSRP)
- HSRP versions
- SNMP (Small Network Management Protocol) and Syslog
- IP Service Level Agreements
- Switched Port Analyzer - SPAN
- Cloud Computing
- SND - Software Defined Networking
- Open SDN and OpenFlow
- Cisco Application Centric Infrastructure
- Cisco APIC Enterprise Module
The VLAN trunking protocol 802.1Q inserts an extra 4-byte (VLAN header) into the original Ethernet frame; of these 4-bytes of VLAN header only 12 bits (called the VLAN ID) identifies the VLAN. These 12 bits (2 to the power of 12=4096) gives a possible number of VLANs from 1 to 4094. The Cisco Proprietary VLAN trunking protocol called ISL (Inter-Switch Link) is less popular than the IEEE certified 802.1Q
(config)#int fa 0/24
(config-if)#switchport mode trunk
(config-if)#switchport trunk native vlan 99
(config-if)#switchport trunk encapsulation dot1q / isl / negotiate
(config-if)#switchport trunk allowed vlan 1-5
(config-if)#in fa0/0.10 ;applicable to router config only
(config-subif)#encapsulation dot1q 10
If while doing PAgP both ends are set to "auto" or LACP both ends are set to "passive", then the trunking will not be established (both ends are on idle waiting for the other end to initiate the trunking negotiation), and the show int switchport will appear as "static access". Cisco recommends to disable trunk negotiation on most ports for better security.
- PAgP (Port Aggregation Protocol), Cisco proprietary) has desirable and auto [remember mnemonic use: I Desire a Powerful car-auto)]
- LACP (Link Aggregation Control Protocol, 802.3ad standard) has active and passive [a mnemonic could be: Go every morning to the LACP to be active rather than passive]
- The mode "on" is the default port-channel mode, working in dynamically negotiation and really should not be use. More info about this on this great blog by Advanxer: https://advanxer.com/blog/2013/08/etherchannel-vs-lacp-vs-pagp/
(config-if)#switchport nonegotiate ;forces the link to be established if other end is passive
#show interfaces trunk
#show interfaces switchport ;very popular command in the exam, get familiar with it!
#show interfaces fa 0/22 switchport
#show etherchannel summary
The following are some commands related to VLANs configuration:
(config)# int vlan 10 ;creates vlan10
(config-if)ip address 192.168.10.2 255.255.255.0
(config)#vlan 10 ;declares an active vlan
(config-vlan)#name Sales
(config-vlan)#int fa 0/22
(config-if)#switchport access vlan 10
(config)#shutdown vlan 10 ;for troubleshooting you can shutdown a whole vlan if you like
#show vlan
#show vlan id 10
#show interfaces fa 0/22 switchport
(config-if)#switchport trunk allowed vlan add 10
(config-if)#switchport native vlan 99 ;set native vlan when the int is in trunk mode
If you have to connect a phone to your switch issue switchport voice vlan 12 or whichever vlan your voice lives on (obviously you need have set the port to access mode, and allow as well the switchport vlan 15 or whichever your lan VLAN traffic is); note that CDP must be enabled on the interface if you happens to connect a Cisco IP phone
VLAN Hooping Exploits; the fact that you can transfer data from one vlan to another without a L3 device, don't rely just on VLANs as your sole means for security
Mismatched Native VLAN
You can set the native vlan in a switch by issuing this command: switchport trunk native vlan 10 ;if two neighbouring switches have different native vlans, this will cause a native vlan mismatch because switches will not add the vlan header to the native vlan when transmitting it through trunks
3. VLAN Trunking Protocol (VTP)
The first thing you need to know about VTP is that IT IS NOT a trunking protocol, the only 2 x trunking protocols are ISL and 802.1Q. VTP should be understood only as a "replication" VLAN protocol; the name of "trunking" comes because this replication protocol only works over trunks connections. There are 3 versions of VTP, though for the CCNA exam only version 1 and 2 are considered. Switches can have 3 x different types of VTP operating modes:
- Server ;allows the creation of vlans that are then advertised using VTP messages through trunks; these messages are sent every 5 minutes and are part of a process called VTP Synchronisation, where all vlan.dat databases files that belong to the same VTP domain are in sync. Whenever there is a configuration change, the switch increases its revision number by 1 and the VTP Sync process starts again in tandems of 5'
- Client ;receive and send VTP messages and modifies its vlan.dat database, but cannot create vlans
- Transparent ;pass VTP messages but does not alter its vlan.dat file; the VTP messages are only passed to switches that have the same VTP version, either 1, 2 or 3; if there is a mismatch of the VTP version, the transparent switch will not forward the messages
For VTP to work, all switches need to be a member of the same VTP Domain, note that the name is case sensitive; the password must also match between the switches. A trunk also needs to exist in between switches; use show cdp neighbors to verify who are your fellows. Note that if a VLAN is shutdown VTP still will announce it as active to neighbours switches
Native VLAN is normally vlan 1; Standard range of VLAN goes from 2 to 1001; Reserved for historical reasons are VLAN 1002 to 1005; Extended range goes from 1006 to 4095 and can only be use when the VTP mode is set as transparent (Server and Client mode only accept normal range).
VTP pruning ;this is the process by which a switch does not flood an interface with VTP info of a vlan that does not exist on the receiving end, for example if of 100 switches only 5 contain vlan 10, VTP pruning ensures that only those 3 switches will received VTP messages regarding vlan 10 and not the other 95. VTP pruning increases bandwidth by restricting flooded traffic
(config)#vtp domain LONDON
(config)#vtp mode transparent ;only passes vtp info
(config)#vtp mode off ;only works on newer IOS, and does not forward any VTP messages
(config)#vtp pruning ;issue this one in the Server type mode switches, so they prune vlans
#delete vlan.dat ;removes all vlan and related VTP info
#show vtp status
#show vtp password
By default, all switches are set to mode Server, meaning they will accept any kind of VTP config setup on the network
Really, the recommended mode is to set them ia transparent, where the switch will not update its vlan database neither will force other switches to do so. If you want to use VTP on your network, ensure you do the following:
- Reset the revision number to 0 of any new switch by doing the following:
- Set it to mode transparent, and then back to either server or client
- Or erase the vlan.dat and then reload the switch
- Always have a VTP domain password in the production environment different from the lab environment
- To enhance security in the switch and prevent DoS attack, either disable the unused ports with the shutdown command, use the switchport mode access or use the switchport nonegotiate so that they never trunk
4. Spanning Tree Protocol (STP 802.1D)
For STP follow the route of configuration, verification and then troubleshooting. STP fixes the issues of Broadcast Storm, MAC Address instability (multiple entries of the same address from different port sources) and Multiple Frame Transmission (the target host is confused when receiving the same frame from different sources). STP works just like when you trace a single path in a living tree from its base to each leaf. STP existed in the times of bridges and hubs, before switches were invented, hence the term use for bridges instead of switches when in the world of STP. This is how STA (Spanning Tree Algorithm) works:
- Hello BDPUs (Bridge Protocol Data Units) are sent where each switch advertises its own BID (Bridge ID), a 8-byte value that contains a 2-byte priority field (defaults to 32768) and a 6-byte that contains the unique MAC address of the switch
- The switch with the lowest BID becomes the root switch (bridge), if they have the same BID, then the switch with the lowest MAC address becomes the root
- All ports in the root bridge are called Designated Ports (DP) and are all in a forwarding state
- Upon receiving Superior Hello BPDUs, the non-root switches now need to select the ports that will become the Root Ports (RP) based on the lowest root cost to the root switch.
- If there is a tie between costs ports on the same switch, then the port with the lowest interface priority number becomes the DP; if both of them have the same port-priority number (which by default is 128), then the one with the lowest interface number wins
- If there is a tie between cost ports on different switches, then the switch with the lowest BID wins, and the other switch will block its port
Notice that, in the connection between an open and blocked port, the port that is open and operational will not populate the MAC address table, as no addresses will come from the other end where the other port is blocked.To tweak the behaviour of STP we have two options to play with: configuring the Bridge ID and/or changing the STP port cost. IEEE defines the STP path cost as follows, where the value is added to the BPDU value received by the neighbouring switch:
- 100 for 10 Mbps
- 19 for 100 Mbps
- 4 for 1 Gbps
- 3 for 2 Gbps
- 2 for 10 Gpbs
(config)#int g1/0/1
(config-if)#spanning-tree vlan 10 port-priority 112
The default port priority is 128 (range from 0 to 255). The above command sets the port priority
of g1/0/1 to 112, hence that port will win if there is a tie
in STP between ports of the same cost
The root switch sends Hello BPDU every 2 seconds by default (which is called the Hello Timer). If a switch stops receiving 10 x Hello Time (MaxAge, which by default is 20 seconds), that switch will start a STP election process and will attempt to change the STP topology. The ports stay 15 seconds on each one of these STP port-states:
| Do not confuse port state (status) with port role | ||
| Port State | STP (15" on each state) |
Port State in RSTP |
| Blocking (Stable status) | does not forward data frames, does not populate MAC address table | Discarding |
| Listening (Transitory status) | as above | n/a |
| Learning (Transitory status) | began learning and populating the MAC addresses table, but still does NOT forward any data frames | Learning |
| Forwarding (Stable status) | does all bits | Forwarding |
| Disabled (Stable status) | does nothing | Discarding |
In STP there are only three port roles (root port, designated port and blocked port), while in RSTP there are five: root port and its alternate port (in non-root switches), designated port and its backup port (in the root switch) and finally the disabled port role
Rapid STP (802.1w)
The MaxAge of RSTP is only 3 x Hello Timer (in other words 3 seconds), thus making convergence quicker. In addition, RSTP introduces two additional port roles:
- Alternate port for non-root switch, to quickly take over the RP in case that fails
- Backup port for root switch, to quickly take over the DP in case that fails
RSTP understand a "point-to-point" port as one that connects to another switch, while a "edge port" is the one that connects to a end device (pc, printer, etc); a shared port is one that connects to a hub, good old days!
per-VLAN Spanning Tree (PVST)
PVST (also called PVST+) is a Cisco proprietary feature that exist for both STP and RSTP; there is also a 3rd type of STP called Multiple Spanning (MST), but that is cover in the CCNP exam. PVST allows you to change the BID and STP port cost per vlan. PVST works by adding a System ID Extension to the BID frame that contain the vlan number, we cannot change it (we can only change the 4-bit priority number)
(config)#spanning-tree mode pvst ;it will show as mode ieee
(config)#spanning-tree mode rapid-pvst ;it will show as mode rpvst
(config)#spanning-tree mode mst
In PVST the BID is set by using the command spanning-tree vlan 10 priority x ; where x must be a multiple of 4096 (4096, 8192, 12288 all the way up to 61440, 15 values only)
To configure the port cost for different vlans on a trunk port, use the command on the interface spanning-tree vlan 10 cost 19 ;if you omit the vlan-id, the cost will apply to all vlans that are going through the trunk
To modify the BID of a switch (which by default is 32768), you can use any of these two commands:
(config)#spanning-tree vlan 10 root primary #configures the switch as primary root
(config)#spanning-tree vlan 10 root secondary #configures the switch as secondary root to take over if primary fails
It is easier to designate a switch as the 'primary' rather than playing around with BID
5. EtherChannel (known as port channel)
Are treated as a single interface as far as STP is concern, and can be of a maximum of 8 ports of equal speed. EtherChannels use load-balancing based on the source MAC address, making a much better use of the bandwidth while reducing the number of times STP has to converge. Both sides have to have the same Speed, Duplex, Mode (trunk or access) and VLANs, and it is recommended to ALWAYS have the interface on shutdown before configuring them with Etherchannel
(config)#interface port-channel 1 ;first create the port channel
(config)#interface range fa 0/1-2 ;select the interfaces to add to the port channel
(config-if)#shutdown ;Cisco recommends to shut b4 configuration
(config-if)#channel-group 1 mode active ;creates bundle group 1 in LACP
(config)#no interface port-channel 4 ;deletes the channel
#show etherchannel summary
It is recommended never to use the “ON” mode (hardcode) otherwise you may not be informed of errors
There are two protocols in use to create an EtherChannel:
- PAgP (Port Aggregation Protocol, Cisco proprietary); mode desirable will force it while mode auto will wait for the other end to start negotiation
- LACP (Link Aggregation Control Protocol 802.3ad); mode active (remember ACtive for lACp) will force it while mode passive will wait for the other end
If you use mode "on", use it in both ends, otherwise you'd be missing protocols (mode "on" creates the etherchannel link unconditionally, without PAgP or LACP negotiation)
PortFast and BDPU Guard
Both of these features should be implemented only on edge ports, so that they are not involved with STP at all (and the edge device becomes functional quickly), preventing loops in case a switch is connected by 'mistake' (BPDU Guard will shut the port down if it detects BPDU frames)
(config-if)#spanning-tree portfast
(config-if)#spanning-tree bpduguard enable
On a 48-port switch with 2 uplinks, instead of manually configuring each int, you can issue the command globally:
(config)#spanning-tree portfast default
(config)#spanning-tree bpduguard default
Troubleshooting spanning tree
(config)#debug spanning-tree events ;will show in the console any STP operations
(config)#spanning-tree mode rapid-pvst ;migrate to use rapid-pvst
The triple A server (Authentication, Authorisation and Accounting) is the IEEE 802.1x standard that authenticates a port before it can transmit packets to the network. The end device that connects to the port must be using an 802.1x client called supplicant, in order to send authentication details; the supplicant is normally part of the OS of the end device
802.1x is an Ethernet protocol but does not use UDP or IP, it uses EAP instead; the supplicant sends the authentication request to the AAA server using an Ethernet frame with an encapsulation called EAP over LAN (EAPoL). Cisco has its own AAA server called Cisco ACS (Access Control Server) that can be installed as an appliance. The AAA server could be using TACAS+ (defined by Cisco) or RADIUS (defined by RFC 28656), and these are the differences:
| Feature | TACAS+ | RADIUS |
| Most used for... | Network devices | Users |
| Transport protocol | TCP | UDP |
| Authentication port number | 49 | 1645, 1812 |
| Protocol encrypts the password? | Yes | Yes |
| Protocol encrypts entire packet? | Yes | No |
| Support function to authorise each user to a specific set of CLI commands of the Cisco IOS? | Yes | No |
(config)#aaa new-model ;enable aaa
(config)#tacas-server host 10.10.10.1 ;specify tacas_+ server
(config)#aaa authentication login default method1 method2 ;uses 2 x methods for authentication
When you enable DHCP Snooping either globally or by vlan, all ports are configured as untrusted (they'll not process dhcp packets generated from DHCP Servers) until they are configured as trusted
To configure DHCP on a switch, do as follows:
(config)#ip dhcp pool Nazaudy
(dhcp-config)#network 10.10.10.0/24
(dhcp-config)#default-router 10.10.10.254
(dhcp-config)#dns-server 10.10.10.70
(dhcp-config)#domain-name nazaudy.com
(dhcp-config)#lease 0 12 ;indicates 0 days and 12 hours
(dhcp-config)#lease 12 ;indicates 12 days
(dhcp-config)#exit
(config)#ip dhcp exclude address 10.10.10.0 10.10.10.80
#show ip dhcp pool
#show ip dhcp binding ;shows the leased IPs
#show ip dhcp conflict
#clear ip dhcp conflict
#ip helper-address 10.10.10.13 ;configure this in the others switches
(config-if)#ip add dhcp ;sets the int on dhcp mode
8. Switch Stacking and Chassis Aggregation
The switches are connected in series, with the last switch connecting again to the first; STP, CDP, VTP and a single MAC address table would run all on the same switch, which is called the stack master.
Cisco FlexStack provides a link of 10GB and run on 2960S and 2960X; Cisco FlexStack-Plus provides 20GB and run on 2960X and 2960XR
In Chassis Aggregation, switches share the power as well as data
There are 2 major types of unitcast IPv6 addresses:
- Global unicast ;work like public IPv4 addresses; their first hex digits are either 2 or 3 (2000::/3 for example)
- Unique local unicast ;work like private IPv4 addresses, their first hex digits are FD
- Link-local address ;similar to APIPA IPv4 addresses (169 range); devices with these addresses do not router packets, they stay always in the local subnet, their first digits are FE80
IPv6 uses the term "prefix" rather than "subnet", and of the 128-bit that compose an IPv6 address, the last 64-bit are the host addresses, where we can do subnetting if needed. Apart from manually assigning an IPv6 to a host, there are 2 ways to do it dynamically (in both situations, the host always learn the DNS server through DHCPv6):
- Stateful DHCPv6 ;a DHCP server will serve IPv6 addresses, however it will never supply the default router, this is done by the client itself through the NDP (Neighbor Discovery Protocol) where the client ask the local routers to identify themselves. The packets to discover a DHCP are sent to the multicast address FF02::2, (using NDP Router Solicitation -RS- messages) and unless a DHCPv6 Rely Agent is configured in the router, the router will block this multicast messages (IPv6 does not broadcast). The DHCPv6 server will reply to the clients with an NDP Route Advertisement -RA- message
- Stateless Address Autoconfiguration (SLAAC) ; in this configuration the client obtain the prefix, prefix length and default router through NDP, and base on that it calculates its own interface ID using EUI-64 rules (for the record, EUI-64 rule is a standard that explains how to change a 48-bit MAC address to a 64-bit IPv6 address)
(config)#ipv6 unicast-routing ;enable IPv6 routing, without this commmand routers will not forward IPv6 messages (NDP, RS and RA)
(config-if)#ipv6 address 2001:db8::1/64 ;configures and IPv6
(config)#ipv6 route 2001:db8::1/64 serial 0/1 FE80::FF:2
The above in the IP Routing table sends traffic to serial 0/1 and the link-local address of the next-hop router
Use ping6 and traceroute6 to troubleshoot IPv6
- #show ip route 2001:db8::1 ;tells you the route that a packet will take to get to that IPv6
- #show ipv6 neighbors ;like the MAC address table in IPv4, it list Ipv6 vs MAC
A computer will use:
- NS (Neighbor Solicitation) message to find out the MAC address of a given IPv6 address
- NA (Neighbor Advertisement) is use by a PC returning a NS request
- RS (Router Solicitation) message to request each router in the LAN to announce themselves along with its IPv6 addresses and prefixes
- RA (Router Advertisement) is sent by the routers with its list of IPv6 addresses and prefix information
By default IOS implicitly permits both NS and NA, but does not automatically permit RS and RA, so ensure there are not ACL blocking them
10. OSPF (administrative distance 110)
OSPF does not use TCP or UDP, it uses instead protocol number 89 to transport IP datagrams. Having router summarisation (10.0.0.0/16 instead of 10.80.20.0/24 and 10.90.60.0/24) makes router tables smaller and easier to manage, therefore summarisation only takes place (or should take place) within an OSPF area. One of the main benefits of creating an area is to enable summarisation
Unlike RIP (which just yell) OSPF has to form relationships with neigbours before exchanging data with them. Each OSPF router flood the network with LSA (Link State Advertisements) until each router has a copy of the LSDB (Link State Database). The best route is calculated using the Dijkstra SPF algorithm
For OSFP to work, first the router needs to have an OSPF Router-ID (32-bit number), which is chosen by selecting the highest active IP address (it is recommended, however, to configure a loopback address and hard code the Router-ID with it, as they never change, and OSPF will default to use it over any other physical address interface). The Router-ID is reset if the router is rebooted and an new interface has been configured with an active bigger IP address (unless, of course, you have configured a loopback address as the Router-ID)
Second, and once the Router-ID is up and running, the router sends OSPF Hellos in order to establish a relationship (hello periods and dead timers must be the same). Once a 2-way relation is established, the router sends LSA (which are nothing but data structures) inside LSU packets (Link State Updates) so each router update their local LSDB with their missing LSA of one another
Finally, the router reflood unchanged LSAs to all their fellows with a default interval of 30 minutes. The DR router is the one that exchanges its DataBase with the other routers. The routers that are not a DR neither a BDR are called DROthers; DRO do not exchange LSDB with each other, they all use the DR as the main point of contact
To form a neighbour relationship between OSPF routers, the following need to match between the two:
- The subnet mask of their network interfaces, obviously, otherwise they won't be able to communicate
- The Hello and Dead timers
- Once every 10 seconds on broadcast, point to point networks, like serial point to point links
- Once every 30 seconds on NBMA (non-broadcast multi access) networks like Frame Relay and ATM
- The Area ID
- The Authentication password
The DR (Designated Router -ALLDRouters- only happens on the same subnet) receives the update at the multicast 224.0.0.6, and then it sends the update to all the members --ALLSPFRouters- using the multicast 224.0.0.5. The DR is chosen by specifying the ip ospf priority n, where the higher number (0-255) the better selection (if not set, whichever has the highest router-id becomes the DR); setting the ip ospf priority of a router to zero will ensure it will never becomes a designated router.[NOTE THIS TRAP!: when loopback address is used, the router-id must be part of one of the networks that is advertised, otherwise no other routers can possibly know your router-id] Once the DR election has occurred, new routers adding to the area (even if they have higher router-id) will not become DR, all of them will need to be turn off/on for the election to start again.
Areas; an area is a set of routers that share the same LSDB, as to reduce SPF calculations (it is recommended to have no more than 50 routers in an area). An ABR (Area Border Router) has connection to at least two OSPF areas
1.(config)#router ospf 1 ;enable ospf in the router with process-id of 1
2.(config-router)#network 10.0.0.0 0.255.255.255 area 10
;tells the router to advertise that network for ospf area-id of 10
show ip ospf neighbor ;shows relationships
show ip ospf database ;show the LSA database, it should display same info for all routers in the same area
show ip ospf route ;show the router IP routes
show ip ospf interface brief ;troubleshoots ospf
1.(config)#router ospf 1
2.(config-router)#shutdown ;this shuts down ospf in the router
A wildcard of 0.0.255.255 tells the router to compare only the first 2 octets of a network, while a wildcard of 0.0.0.255 tells the router to match and compare the first 3 octets; the command network 0.0.0.0 255.255.255.255 will match all IP addresses
(config)#interface loopback 0
(config-if)ip address 2.2.2.2 255.255.255.0
The above configures a Router-ID of 2.2.2.2
If you don't want OSFP announcements to be sent via a a particular interface, you can use ospf passive interfaces in two different ways:
- (config-router)# passive interface default ;sets all interfaces as passive interface (you'll do this if, let's say, the router has 24 interfaces and you want to enable ospf only in 2 of them), then you need to go to the interface you want to set as active and do:
- (config-router)#no passive interface f0/0
- (config-router)#no passive interface f0/1 ;only configures that 'specific' interface to be passive, while all other ones will be involved in ospf routing
Once the interface is in passive, the router will stop listening or sending ospf hello messages, and will stop forming any neighbour relationship over that interface
#sh ip ospf int br ;list all ospf interfaces including the 'passive' ones
#show ip route
0 172.16.1.1/32 [110/151] via 10.10.10.1 ;110 is the AD (Administrative Distance), while 151 is the metric of that route
OSPF default route; it is handy to have an OSPF default route in all areas, being this default route the one where the internet traffic should go (ip route 0.0.0.0 0.0.0.0 192.168.0.1). To achieve this, issue this command on the router that directly connects to the Internet
(config-router)#default-information originate
The metric use by OSPF is cost calculated by its bandwidth by the formula 100,000/interface_bandwidth in kbps; to change the cost of an interface you can issue the command ip ospf cost x or you can modify its bandwidth by issuing bandwidth 10000 for example, which will result in a OSPF cost of 10 (100,000/10,000= 10)
- 128 Kpbs cost 781
- 348 Kpbs cost 266
- 768 Kbps cost 133
- 1.544 Mbps (T1) cost 64
- 44.736 Mbps (T3) cost 2
- 10 Mbps cost 10
- 100 Mbps cost 1 (this is the speed reference for OSPF)
- 1 Gpbs and above, all cost 1
To modify the reference bandwidth value from the default of 100,000 (which is 100Mbs) use the command auto-cost reference-bandwidth 10,000 ,where 10,000 is equal to 10Gpbs as this command treats the reference value in Mbs rather than Kpbs
(config-router)#maximum-paths 6 ;in case you want to load balance traffic between 6 routes,the default value is 4
(config-if)#ip ospf 1 area 20 ;this is another way to enable ospf on the int,
instead of the "network" command you specify the corrects ospf process + area
(config)#clear ip ospf process ;resets all relationships
(config)#no router ospf 1 ;bye bye
Useful links about OSPF
IPv6 with OSPF
IPv6 is implemented through OSPFv3, which does not use the network command, it uses interfaces configurations instead. OSPFv3 has a feature called address families that allow you to run the router in dual stack, supporting both IPv4 and IPv6, though each protocol still will have its own separate link-state database (LSDB), separate messages, SPF calculations and processes. Some of the stuff that OSPFv2 and OSPFv3 have in common are:
- Both use the same metric concept of cost of each interface
- Both perform a number of checks before routers become neighbors
- After they become neighbors, both proceed to exchange the contents of their LSDB that describes the network topology in between the two
- After all LSAs messages have been exchanged, both use the shortest path first -SPF- algorithm to calculate the best route to each subnet
1.(config)#ipv6 router ospf 1 ;enable ospf in the router with process-id of 1
2.(config-router)#router-id 2.2.2.2 ;sets the router-id
3.(config-router)#ipv6 ospf 1 area 23 ;enable ospf with process-id of 1 in area-id 23
Passive-interfaces, load-balancing and router-id use exactly the same commands as OSPFv2 (yes, in OSPFv3 the router-id is a 32-bit number). The same applies to the command default-information originate, that needs to be configured on the IPv6 router facing the Internet so that it can route packets to the web. Of course, in OSPFV3 router-id must be unique and hello/dead timers must match
The DR router send messages updates to all OSPFv6 routers to the multicast FF02::5, then receive updates from all DR and BDR routers through the FF0::6 address, much like IPv4 224.0.0.5 and 224.0.0.6. Remember that OSPFv3 neighbours do not have to have their IPv6 in the same subnet for them to establish a relationship, while on OSPFv2 their IPv4 addresses must be on the same subnet
If you can't run show running-config, use these to find the int where OSPF have been enable:
#show ipv6 protocols
#show ipv6 ospf interface
#show ipv6 ospf interface brief
#show ipv6 ospf neighbor
#debug ipv6 ospf adj ;shows events when neighbors work through their states, which could be full (if the router is a DR or BDR)
or 2-way state (if the router is a DROther)
#clear ipv6 ospf process ;reload ospf
The Maximum Transmission Unit (MTU) issue
Both OSPFv2 and OSPFv3 experience an issue by which routers are able to establish an OSPF relationship but then fails in exchanging database due to mismatch in their MTU interface. They fail with the error "Too many retransmits"; you can set the MTU on an interface by using ipv6 mtu 1500 or ip mtu 1500
#show ipv6 route ospf
OI 2001:DB8:1:4::/64 [110/129]
via FE80::FF:FE00:1, Serial 0/0/0
In the above excerpt, the "I" identifies the route as an interarea OSPF route,
If it was an intra-area (within the same area) it will display only "O"meaning it has been learnt through OSPF
11. EIGRP (administrative distance 90)
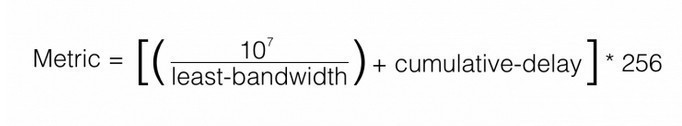
EIGRP can be much simpler to implement than OSPF; it sends only partial updates (to the multicast address 224.0.0.10) and does not require 2 neighbouring routers to have the same Hello and Hold interval (though this is highly advisable, otherwise one router may believe the other one has failed due to its slow response, and use an alternative path for its routes). The metric use by EIGRP to calculate routes is a composite of bandwidth and delay in a formula that uses the units in tens of microseconds. The formula for EIGRP is really composed of more criterias, K1 to K5, though only K1 and K3 (bandwidth and delay) are set to 1, the other K values (reliability, load and MTU) are set to zero
Split horizon ;the router will not send advertise updates through an interface when those updates have been learnt through that very same interface
Route poisoning ;the router will advertise a route with a metric of infinite if that route has failed; for RIP the infinite is a value of 16, while EIGRP has a value of 2 power of 32 minus 1 and OSFPv2 has it for 2 power of 24 minus 1
For 2 x EIGRP routers to form a relationship and exchange updates/topology information, they need to agree first on the following:
- Authentication process must be the same (password)
- Autonomous System Number (ASN) in use must be the same
- The Hello updates must be on the same subnet (obviously)
EIGRP updates use the RTP (real-time transport) protocol for communication, instead of UDP or TCP, so that they know if an neighbour has received and update or not. Full updates only occur when the router comes up, after that there is only partial updates
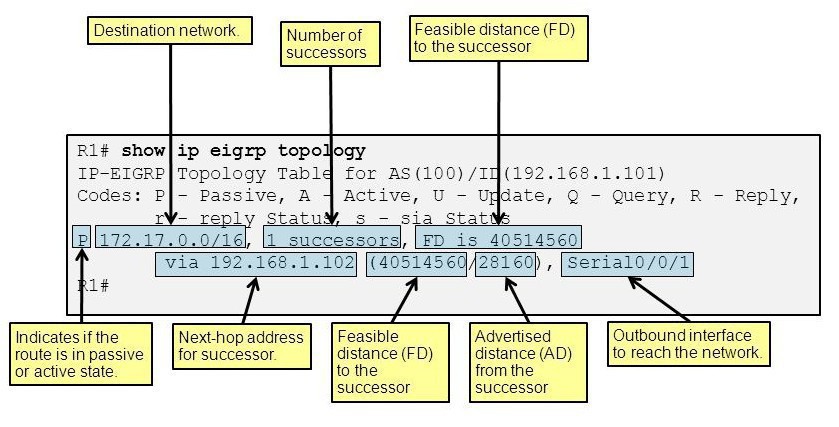
Convergence ;for each subnet, the router calculates the best path and call that route a successor for that particular subnet, adding it to the routing table and the topology table. At the same time, the router calculates and alternative, loop-free path to the same subnet called a feasible successor, and add it only to the topology table, and have it at hand just in case the successor route fails. Don't confused feasible distance (FD) with feasible successor, a feasible distance is the distance to the successor not the feasible successor itself.A router reported distance is the metric of a route from the neighboring router's perspective
If a route fails, and there is no feasible successor available, the router uses the Diffusing Update Algorithm (DUAL) to choose a replacement route; DUAL will send queries looking for a loop-free route, and once founded it will be added to the routing table
(config)#router eigrp 10 ;configures autonomous system number (ASN) as 10
(config-router)#network 10.10.0.0 ;eigrp starts advertising that subnet
(config-router)#network 10.10.3.0 0.0.0.255 ;advertise only a specific interface/subnet
(config-router)#variance 2 ;with interger 2, it multiplies the FD by 2, then any
feasible route that is less or equal to the result FD x 2 is added to the routing table.
Routes that are neither Successors nor FS can never be added to the IP routing table.
#show ip protocols
#show ip route
#show ip route eigrp
#show ip eigrp interfaces ;great for troubleshooting
#show ip eigrp protocols
#show ip eigrp neighbors
#show ip eigrp topology all-links ;list all routes
#show ip eigrp topology ;list both successor and feasible successor routers
#debug eigrp fsm ;shows you the events regarding eigrp
#show ip eigrp traffic ;view the number of EIGRP packets that are sent/received
(config-if)#bandwith xxx
(config-if)#delay xxx ;these configure the two main metrics use by EIGRP
Nowadays, people will avoid to use auto-summarisation so that routes are advertised with their correct subnets and not with subnets A, B or C; this is specially true when some of the subnets that are autosummary are discontiguous
(config-router)#no auto-summary
Useful links about EIGRP
- https://www.computernetworkingnotes.com/ccna-study-guide/eigrp-metric-k-values-explained-with-examples.html
- http://kwallaceccie.com/eigrp-2/
- http://slideplayer.com/slide/6224122/
IPv6 with EIGRP
EIGRP IPv6 use the multicast address FF02::A to send messages. The main difference between EIGRP IPv4 and IPv6 is that IPv6 does not support the network command, instead you use (config-if)#ipv6 eigrp as-number to configure that interface for EIGRP IPv6. For v6 there is no the autosummary concept, they advertise prefixes (instead of subnets like in IPv4) and routers can become neighbours even if they are in different IPv6 subnets (unlike IPv4)
1.(config0#ipv6 unicast-routing ;don't forget to enable IPv6 routing fist
2.(config)#ipv6 router eigrp 1 ;defines as-number as 1
2.(config-router)#eigrp router-id 1.1.1.1 ;sets router-id
4.(config-if)#ipv6 eigrp 1 ;makes that interface participant in eigrp
To configure EIGRP in a router to have at most 5 routes with a variance of 4 for unequal cost routes, you'd use the same command as if with EIGRP IPv4:
(config-router)#maximum-paths 5
(config-router)#variance 4
To set the Hello timer of an interface to, let's say 7 seconds, you'd use the same command as in IPv4 but replacing ip for ipv6
(config-if)ipv6 hello-interval eigrp 1 7 ;that sets the hello to 7 seconds for as-number 1
Having different router-ids in EIGRP IPv6 does not prevent routers from becoming neighbours, but can cause problems when external EIGRP routes are added to the routing table. They must however always be on the same ASN number
12. BGP (Border Gateway Protocol)
BGP advertise routes in between ISPs by exchanging public IP Subnets, which in BGP are called NLRI (Network Layer Reachability Information). BGP does not use metrics, instead it uses a process called "path selection" that work through a series of comparison (about 10) between routes. One of these comparisons attributes is "AS_Path" that works like hop count but between ASN areas
- eBGP ;externalBGP advertise routes between ASN -Autonomous System Numbers-
- iBGP ;internalBGP advertise routes inside and within ASNs
The type of Internet connection an Enterprise could have to their ISP is Single Home (a single cable), Dual Home (2 cables but to the same ISP, this add redundancy if a cable is cut), the popular cost-effective Single Multihomed (one cable to one ISP and another cable to another ISP) and the top-notch Dual Multihomed (2 cables to one ISP and another 2 cables to a different ISP)
When you configure BGP it open port TCP 179 waiting for incoming connection requests from other routers; after the connection is established and some checks are passed, the routers become BGP peers (neighbours) and start exchanging routing information
(config)#router bgp 1001 ;enables bgp for ASN 1001
(config-router)#neighbor 195.12.50.2 remote-as 102 ;establish a peer with router 192.15.20.2 for ASN 102
(config-router)#neighbor 195.12.50.3 shutdown ;administratively disables this peer router, which will make its neighbor status as "idle Admin"
(config-router)#network 192.0.2.0 mask 255.255.255.0 ;inject this network in the bgp table
(config-router)#aggregate-address 192.168.5.0 255.255.252.0 summary-only
The above command summarise all subnets in 192.168.50.0/22, if you ommit the "summary-only" command, the subnet is added but obviously not summarised
If you need to advertise two routes that have been subnetted, the best way is to enter a null0 interface for the main subnet mask, something like this will allow subnet /32 and /29 to route okay:
ip route 192.0.2.0 255.255.255.0 null0
sh ip bgp summary ;for troubleshooting
sh ip route 200.1.1.0 255.255.255.0 longer-prefixes ;list all subnets defined in the range, if any
Useful links about BGP
- http://bgp.potaroo.net/
- https://www.cisco.com/c/en/us/support/docs/ip/border-gateway-protocol-bgp/5441-aggregation.html
PPP is a common layer 2 protocol for WAN that has two components: LCP, which negotiates the connection, and NCP, which encapsulates the traffic. To establish a communication between 2 x routers through the PPP protocol, do as follows:
(config-if)#encapsulation ppp ;do this at the serial interface
(config-if)#ppp authentication chap ;do this if you want to use chap
(config-if)#ip address 192.168.0.1 255.255.255.0
R1(config)#username R2 password letmeinnow ;do the reciprocal thing in the other router
#show ppp all
#show interfaces serial 0/0 ;for troubleshooting
MLPPP (MultiLink PPP) is a method by which 2 x routers are connected using 2 x serial cables for redundancy, forming a sort of EtherChannel which, operating at layer 3, is called MLPPP. This is how to configure it:
(config)#interface multiink 1 ;creates a new multilink interface,
you need to run this in the 4 x serial interfaces,
and the multilink group number (on my example 1) must be the same in all of them
(config-if)#encapsulation ppp
(config-if)#ppp multilink
(config-if)#ip address 192.168.0.1 255.255.255.0
(config-if)#ppp multilink group 1
Now, on each of the physical serial interfaces, you issue these commands,notice that there no IP address for the physical, only for the virtual multilink
(config-if)#encapsulation ppp
(config-if)#ppp multilink
(config-if)#no ip address
(config-if)#ppp multilink group 1
(config-if)# (any authentication command is needed)
When you issue show interfaces on a router, look for the "keepalive" entry and ensure that it is set (10 sec is the default)
#debug ppp authentication ;to troubleshoot authentication
#show ip route
Use these commands to test frame-relay after implementation:
#show frame-relay lmi ;display traffic LMI stats
#show frame-relay pvc ;display status and traffic stats of configured PVC
#show frame-relay map ;display map entries about the connections
Metro-Ethernet operates mostly in 3 ways:
- E-Line, similar to Point-to-Point and referred by the name "Virtual Private Wire Service" ;it is a cable in between two sites that pass through the Service Provider, the network between the site customers is called EVC (Ethernet Virtual Circuit), and it could be layer 3
- E-LAN, similar to full mesh and referred by the name "Virtual Private LAN Service" ;it consists of several customers routers connected to the same EVC, they are all part of the same subnet so that they exchange routing to one another
- E-Tree, similar to hub-and-spoke, the good old design of Headquarters (the tree) connecting to the branches (the leaves). In a layer 3 design normally the tree router will have subinterfaces with each one of then servicing the branches routers. Point-to-Multipoints and Partial Mesh are also designs that falls into this category
Committed Information Rate (CIR) is the speed the Service Provider can give you, let's say a 200MBs over a 1GB line; to ensure the customer don't suppress the 200MB (CIR), the service provider will use policing and will drop frames if the ingress is over the agreed rate. The customer can use the QoS tool called Shaping to ensure their routers send the frames just at the CIR speed, so that no frames are dropped but rather held in a queue
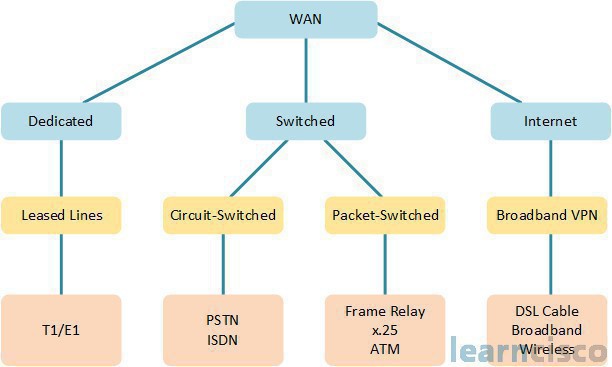
MPLS (Multiprotocol Label Switching) is a layer 3 WAN service that, unlike VPN, offers no encryption, and packets of different customers are all inside the same Service Provider but isolated from one another thanks to their label. For a MPLS network, the following applies:
- The Service Provider (SP) needs to know the customer's IP addresses
- Some kind of IP routing protocol is run to make forwarding decisions between the customers subnets
On a MPLS network you have the Customer Edge (CE) router and the Provider Edge (PE ) router. QoS is provided by a value called DSCP EF that recognizes VoIP packets and prioritize them in the MPLS network, but both customer and provider need to liaise to take the most of VoIP and define its functionality; the SP may even need to advertise the customer router across the WAN (the routing protocol of choice must be agreed, etc)
The CE routers will establish relationships only with the PE routers (not with others CE routers, in spite of them being part of the same company);in order for the PE routers to advertise the customer routes, the PE routers use a process called route redistribution that happens inside a router, where routes from one routing protocol are injecting into another; within the PE routers the route redistribution happens thanks to a routing protocol called Multiprotocol BGP (MPBGP), able to advertise routes from multiple customers while keeping the routes logically separated.
When OSPF is in use for the MPLS, it creates a super backbone (normally Area 0) in between the PE routers, while each CE routers (or group of single-linked routers) and the PE routers form a designated area. When using EIGRP on a MPLS network, the ASN numbers does not need to be the same between each branch CE router, and if it happens to be the same the whole PE network will be transparent to EIGRP routing
DLSAM ;DLS Access Multiplexer is a device of the Telcos (Telephone Companies) that splits the signals between digital data (destined to a router) and analog voice (destined to a voice switch)
ADSL ;Asymmetric Digital Subscriber Line offers faster download speed for the customers but lower upstream. Note that a DSL connection speed is degraded the further it goes from the Telco CO (Central Office)
VPN ;a VPN connections offers Confidentiality, Authentication, Data Integrity and Anti-Replay
IPSec ;provides encryption to the data
15. GRE Tunnels and DMVPN (Dynamic Multipoint VPN)
GRE defines a complete 20-byte IP header called the "delivery header". To create a GRE tunnel between 2 routers that are connected to the Internet and each one has a public IP address exposed to the outside world, do as follows:
1-(config)#interface tunnel x ;where x is a local number that does not need to match between routers
2-(config-if)#tunnel mode gre ip ;tell IOS to use GRE encapsulation over the tunnel
3-(config-if)#ip address 10.10.10.1 255.255.255.0 ;give a private IP to the tunnel
4-(config-if)#tunnel source g1/0 ;specify the int/local ip that will be use by the tunnel
5-(config-if)#tunnel destination 100.100.100.1 ;put the public IP of the peer router
On the peer router, do the same but different
1-(config)#interface tunnel x
2-(config-if)#tunnel mode gre ip
3-(config-if)#ip address 10.10.10.2 255.255.255.0
4-(config-if)#tunnel source g1/0
5-(config-if)#tunnel destination 200.200.200.1
To check the config, use:
#sh int tunnel x ;should show up/up
#sh ip route

When using ACLs, note that routers do not filter packets that they themselves create, so look at the incoming rules for ACL and ensure GRE traffic is permitted; GRE is not UDP or TCP therefore the ACL needs to specifically permit it with the command "permit gre any any" applied to a extended ACL
Multipoint VPNs with GRE can cause the central site configuration to get large and complex due to per-channel configuration of every remote child site. The Cisco Dynamic Multipoint VPN (DMVPN) IOS feature solve this problem by implementing a protocol called Next Hop Resolution Protocol (NHRP) in which one router (the spoke) act as a NHRP server maintaining a NHRP table with all the other client routers mappings
Before sending the frames over a physical link, the routers encapsulate the frames inside various headers: tunnel header, PPP header and IP packet. PPPoE connects 2 x routers over an ethernet cable with no IP address, so that the connection works over Layer 2; you first create a dialer pool and then add the physical interface to that pool
1.(config)#interface dialer 1 ;creates the dialer, on this example with the number 1
2.(config-if)#ip address negotiated
3.(config-if)#mtu 1492 ;prevents fragmentation
4.(config-if)#encapsulation ppp
5.(config-if)#ppp chap hostname Router1 ;sets the chap authentication, needed!
6.(config-if)#ppp chap password LetMeIn
7.(config-if)#dialer pool 1 ;creates pool to which you later will add the physical int
After the above steps, do this on the physical interface:
1.(config)#interface g0/1
2.(config-if)#no ip address
3.(config-if)#pppoe-client dial-pool-number 1 ;adds the int to the dialer poool
4.(config-if)#pppoe enable ;this command is added automagically by the router when using pppoe-client
5.(config-if)#mac-address 0123.0456.0789 ;this is optional
6.(config-if)#not shut ;obviously
While the physical doesn't, the dialer interface does need an IP address, the command ip address negotiated tells the other router (the ISP router) to use PPP IP rather than DHCP. If for the contrary the ISP has given you an IP address, use it instead. The command mtu 1492 prevents unnecessary packet fragmentation as PPoE adds an extra 8-byte to the IP packet header which MTU normally defaults to 1500
The following is an example of how an ISP router would be configured at the other end of the PPoE, the CCNA exam only cover the PPoE client side:
ip local pool TestPoool 10.10.10.2 10.10.10.254
bba-group ppoe TestGroup
virtual-template 1
username Admin password LetmeIn
interface virtual-template 1
ip address 10.10.10.1 255.255.255.0
peer default ip address pool TestPool
ppp authentication chap LetMeIn
interface g0/2
no ip address
pppoe enable group TestGroup
no shut
mac-address 0100.0200.0300
The physical interface sends Ethernet frames, the virtual-access interface sends PPoE frames (over the physical one) and the dialer interface sends IP packets (layer 3 over the virtual-access interface). To test and verify PPoE you can use these commands
#show interfaces dialer 2 ;you should see "up spoofing" meaning normal operation
#show interfaces virtual-access 2 configuration
#show running-config inteface dialer 2
#show ppoe session
#show ip route ;you should see the dialers directly connected
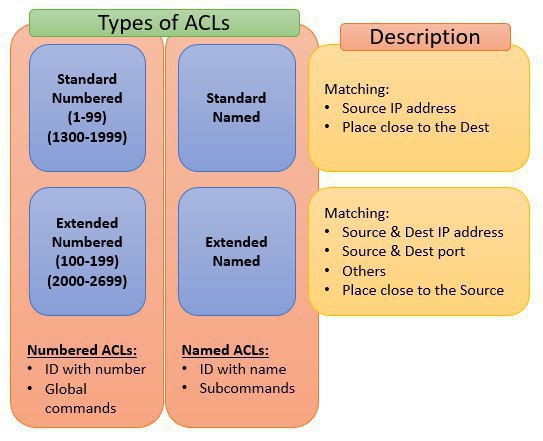
These are the types of ACLs, where Extended ACLs have a more robust ability in matching packets than Standard ACLs. IOS allow standard ACLs to match a range of addresses using a tool called a wildcard mask (note that the wildcard -wc- is NOT a subnet mask), for example, for subnet 255.255.252.0 the wildcard mask will be 0.0.3.255, where every bit that is "on" in the octet will be ignored (not processed) by the ACL router
All ACLs end up with a deny all command, if you would like to override this behaviour issue the command access-list 1 permit any at the end of the ACL. If on the other hand you want to see and count the number of packet that get denied by the router, list the command access-list deny any at the bottom, this will display the number to matches packets when issuing show access-list; this is because the invisible implicit deny all command does not log
Remember that, with an outbound ACL, a router does not filter packets that the router itself creates. The limitation of Standard ACLs is that they cannot check the destination IP address, while Extended ACLs can check both source and destination. Here, have a look at some example for configuring Standard ACLs:
(config)#access-list 1 permit 10.10.10.1 0.0.0.255
(config)#access-list 1 remark Allow traffic from host 0.1 ;this is a comment
(config)#interface ga 0/0
(config-if)#ip access-group 1 in ;apply the ACL to the desired interface
For troubleshooting, you can use this lot:
#show ip access-list ;list details of IPv4 ACLs only
#show access-list ;list details of IPv4, IPv6 and others ACLs
#show ip interfaces
#show ip interfaces | include list
Extended ACL can examine multiple parts of the packet header, making them more useful and complex than Standard ACLs; both use the access-list command which requires 3 matching parameters: the IP protocol type (udp,tcp,icmp,etc), the Source IP address and the Destination IP address. When matching a single IP address, the extended ACL requires the use of the host keyword
Automatic sequence Numbering; IOS adds sequence numbers to commands as you configure and grow the ACL statement, allowing you to delete those command lines individually. To do so issue the command do show ip access-list 101 and then the no 30 or whichever line you wish to remove
Cisco recommends to disable (use the no ip access-group) an ACL from its interface before making any changes to the ACL; among the well-know recommendations of Cisco regarding ACLs are:
- Place the more specific statement early in the ACL processing
- Place Standard ACL close the the Destination, to avoid mistakes of discarding packets that were meant to be allowed
- Place Extended ACL close to the Source, to save bandwidth and discard packets early
Thinking about ACL configuration, is the best way to troubleshoot problems with ACLs, specially when you consider that ICMP packets may be allowed but everything else blocked by the implicit denied statement, making you think that all is working okay. Follow this broad guidelines to troubleshoot problems:
- Find out the location and direction of the ACL; use show ip int g1/0/1, show access-lists, show ip access-lists (useful counter when traffic is generated) and /or show run
- Understand the ACL, look for misordered statements, reverse source/destination IP address and common syntax mistakes
- RIPv2 uses the well-know UDP port 520, so ensure this is specifically allowed if using RIPv2. To allow OSPF and EIGRP you use the respective ACL protocol keyword ospf and eigrp
- Remember that a router will always bypass any outbound ACL for packets that it itself originates, this applies to packets of ping, traceroute and routing protocols
ACL in IPv6
The IPv4 and IPv6 ACL statements are not exchangeable, and likewise IPv4, ACLs IPv6 match agaist IPv6 addresses and fields that are unique (flow level, DSCP, etc) to an IPv6 header. These are the key differences between the two:
- ACLs IPv6 use names only (unlike names and numbers that are both present in IPv4)
- ACLs IPv6 have the same concept of standard and extended ACLs, but they do not differentiate their styles with the configuration keywords of "standard" or "extended"
- Just before the deny all statement, ACLs IPv6 have a implicit permit statement at the end of each ACL, while IPV4 just don't
Remember that the most secure configuration method is to use inbound ACLs on the interfaces the face the unstrusted network, so that the router can block incoming packets before they get into the lan. Always have a "fail-safe stance", meaning to only permit what you want and block everything else.
ICMPv6 Caution; while in IPv4 you normally will block ICMP packets, the ACLs in IPv6 need to have the traffic of ICMP allowed, because there are services like NDP (Neighbor Discovery Protocol) and PMTUD (Path MTU Discovery) that use them. Consider also the following when working with ACLs IPv6:
- Matching Tunneled Traffic ;to communicate two islands of IPv6 over an ocean of IPv4, you would send the IPv6 packets encapsulated (with GRE) over a tunnel; this will result in the ACLs unable to filter those IPv6 when they are inside IPv4 packets
- IPv4 wildcard mask and IPv6 prefix length ;in IPv6 the prefix length number represents the number of contiguous bits that will be matched for the IPv6 address prefix, just like in IPv4
- ACL logging impact ;as always, take care wit any ACL statement or entries that uses the word log, it can clock the system. In ACL IPv6 the logs are created for the first packet and then in every 5-minute interval, but even so be aware of its CPU demand
While IPv4 uses the ip access-group command, in ACL IPv6 this command is replaced by ipv6 traffic-filter an then the "in" or "out" depending on the direction you want to apply the ACL for
1.(config)#ipv6 access-list LAN_5 ;create ipv6 acl with the name "LAN_5"
2.(config-ipv6-acl)#permit ipv6 any 2001:db8::2/64
3.(config-ipv6-acl)#int s0/0/1
4.(config-if)#ipv6 traffic-filter LAN_5 in ;notice the "in" for inbound at the end
There is no difference between standard and extended ACLs type in IPv6, an extended IPv6 ACL simple uses more commands for its statements, obviously more than the destination IP address that defines a standard IPv4 ACL. The following example will configured a host to a web to permit ssh traffic (and, of course, ICMPv6 for IPv6 to work)
1.(config)#ipv6 access-list SS_TO_HOST5 ;create ipv6 acl with the name "SS_TO_HOST5"
2.(config-ipv6-acl)#permit tcp 2001:db8::2/64 2001:db8::5/64 eqqq 22 log
3.(config-ipv6-acl)#permit icmp 2001:db8::2/64 2001:db8::5/64 eqqq echo-request log
3.(config-ipv6-acl)#int s0/0/1
4.(config-if)#ipv6 traffic-filter SS_TO_HOST5 in
Use show ipv6 access-list to troubleshoot as well as to show ipv6 routers. There are 3 implicit ACL rules at the bottom of every ACL IPv6: permit icmp any any, permit nd-na any any ,and deny ipv6 any any; the purpose of this is to allow Neighbor Solicitation (NS) and Neighbor Advertisement (NS) messages
Cisco provides a range of QoS tools on both routers & switches to manage four characteristics of network traffic:
- Bandwidth; the capacity of the link, how many bits can be send per second
- Delay; can be described as one-way delay (the time it takes for packet A to arrive to destination B) or round-trip delay (the time it takes packet A to get to destination B and back again to destination A). For interactive voice the tolerated delay (one-way) is 150ms or less, while for video is 200ms to 400ms
- Jitter; is the difference of delay between packets, for example, if one packet has a delay of 100ms and the other one has a delay of 120ms, then the jitter between these two packets is 20 ms. For interactive voice traffic the recommended jitter is 30ms or less, while for video is 30ms to 50ms
- Loss; dropped packets can be cause by faulty cables, poor WAN services or router/switch congestion, where the packets accumulates waiting to be send and the device drops them. For voice the loss could be 1% or less, while for video the guideline is to keep the loss under 1%
Like ACLs, QoS tools can be enabled on an interface, for one or another direction. The company needs to create a QoS plan and decide which traffic they want to prioritise. Cisco uses specific tools to tackle QoS, these tools are organised in the following sections:
Classification and Marking
Cisco recommends doing complex matching early in the life of a packet (when it is generated), and then mark the packet for QoS if needed. That way when the packet travel through the network all devices look at the mark and prioritise it accordingly. The Type of Service (ToS) is a byte in the IPv4 header that contains a 3-bit (8 possible values) IP Precedence (IPP) and the 6-bit (allowing for 64 unique values) Differentiated Services Code Point (DSCP). The packet is marked normally using the DSCP. This method works like an ACL, but for more complex classification & matching of applications signatures you can use Cisco Network Based Application Recognition version 2 (NBAR2), allowing you to classify traffic for a specific service like, let's say, WebEx. This is a list of the most common marking fields and the header where they exist:
| Field Name | Header | Lengh in bits | Where used |
| DSCP | IPv4, IPv6 | 6 | End to end packet |
| IPP | IPv4, IPv6 | 3 | End to end packet |
| CoS | 802.1Q | 3 | Over VLAN trunk |
| TID | 821.11 | 3 | Over Wi-Fi |
| EXP | MPLS Label | 3 | Over MPLS WAN |
Trust Boundaries is a point from which QoS marking is trusted, any packet marked for QoS process beyond the trust point is not trusted; IP phones and/or switches normally define this boundary
- Expedited Forwarding (EF) is a DSCP value with decimal 46 for packets that need low latency (delay), low jitter and low loss. By default Cisco IP Phones mark voice payload with EF
- Assured Forwarding (AF) is a set of 12 DSCP values that defines 4 separate queue, each one of them with a different level of priority
- Class Selector is a set of 8 DSCP values for backward compatibility with IPP
Congestion Management (Queuing)
The router/switch held packets in different queues, then use prioritization to give priority to packets held in one queue over the others.
- Round Robin Scheduling; round robin is an algorithm use by Cisco by which some packets are moved up in the queue
- Cisco-Based Weighted For Queuing (CBWFQ) is a tool by which certain queues are reserved a designated amount of dedicated bandwidth all the time
- Low Latency Queuing (LTQ); used for voice and video, it tells the scheduler to treat one or more queues as special priority queues, incurring in very little delay and jitter for packets in that queue
Shaping and Policing
The Shaping & Policing tools in QoS are use in WAN connections, at the edge in between 2 networks. They monitor the bit rate that flows through a device, discarding excess traffic in an attempt to keep the bit rate at or below the configured speed. For example, if you have a 1Gps bearer link but only a 200MB CIR (committed information rate) you'll use shaping to tune traffic at 200MB. This inevitably lead to delay and jitter, and to prevent that Shaping uses a short time interval to support voice and video
Congestion Avoidance
The TCP window size is the number of bits a sender can send before expecting a TCP acknowledgement for those bits; with every new acknowledgement a new window (with the same size) is granted. The size of the window changes when there are segment lost. In case of congestion we run into a problem called "tail drop", by each the last packets of the window size are dropped as there is no room in the queue for more. In QoS, congestion avoidance tools like better DSCP marking, come into action when packets are being dropped
Both router-on-a-stick (ROAS) and layer 3 switches with switched virtual interfaces (SVI) will use sub-interfaces to router inter-vlan traffic. Remember that the native vlan is not tagged over trunks, therefore ensures that the native vlan is matched between switches.
(config-if)#encapsulation dot1q 10 native ;use this command to configure vlan10 as the native one
#sh ip route connected ;to veriy the ROAS configuration
Note that a layer 3 will need an interface on each VLAN, plus another interface (in access mode, not trunk) linked to the outside router for Internet traffic. To enable IP routing in a layer 3 switch do as follows (the sdm prefer commands allocates space for the routing tables):
1)#show sdm prefer ;first verify the mode in which the switch is
2)(config)#sdm prefer lanbase-routing ;switch to forwarding
3)#reload
4)(config)#ip routing ;enable it after the reload
In a switch use the no switchport in the physical interface to disable switching and enabling the port as a router interface instead (notice that when this command is added, IOS add the no ip address to the interface, this is so that the IP is configured in the port-channel interface only). If the physical interface is linked to a port-channel, do the same thing in the port-channel, add the no switchport command to make sure the Po1 act as a routed port. Once you're done, use the command show etherchannel summary and see if the (R) -layer3/routed- is added to the Po1 instead of the (S) -switch-
- Remember that, when bundle interfaces in port-channels, they must have the same speed and duplex configurations
- Routers have by default the ip domain-lookup configured but with no DNS address set, therefore you should either add a DNS to the router (so that it resolves names) or disable dns resolution on the router by issuing the command no ip domain-lookup
- Configure the (config-if)# ip helper-address dchp-server-ip so that the router will pass the DHCP broadcast for that particular interface to the DHCP server located in another subnet
- An interface will be in a down/down state if its speed doesn't match the one at the other end
- The "rule of specificity" always applies when deciding how to route packets: the router will always choose the path with the largest prefix (/30 over /28) as it is more specific. After this rule is applied, the router then use the route with the lowest AD number
- The 0.0.0.0 network address and mask 0.0.0.0 is called the quad-zero route
- (config)#ip route 192.168.3.0 255.255.255.0 192.168.1.1 ;instruct the router to use the next hop IP (192.168.1.1, which is the IP of another connected router) in order to reach the network 192.168.3.0
- (config)#ip route 172.16.3.0 255.255.255.0 serial 0/0/0 ;instruct the router to use its interface serial 0/0/0 in order to reach the network 172.16.3.0
- #ping 192.168.0.1 source 192.168.1.1 ;this command instruct the router to ping the address 192.168.0.1 but using the interface connected to 192.168.1.1, nice command to know for troubleshooting
- (config)# router ospf 23 ;configures the router to use ospf, with the process id of 23, this process id is enterely your choice
- #show ip arp ;displays the arp tables of the switch/router, matching IP address with MAC addresses
Interior Gateway Protocols (IGPs) are RIPv2, EIGRP and OSPF; they route within a single Autonomous System (AS), a collection of networks. IGPs can further be divided as follows:
- Distance vector (RIP); use a metric such a hope count, and they send the whole routing table on the updated (RIPv1 used to)
- Advance distance vector (EIGRP); uses a Hello protocol to discover neighbors to whom it establish relationships and periodically sends updates, which are partial and send only when a change occurs
- Link-State (OSPF, IS-IS); uses the SPF algorithm to create an abstraction of the exact topology map of the entire internetwork. All link-state routers use its own internal map of the network and calculate the shortest paths to reach the destination network in relation to where they are on the map. Link State Advertisement (LSA) are sent periodically, every 30' by default and to the multicast address 24.0.0.5
Exterior Gateway Protocols (EGPs) are design for use between Autonomous Systems that are under the control of different administrations; BGP -border gateway protocol - is an example.
Administrative Distance of Routing Protocols:
- 0 - Directly connected interface
- 1- Static route that has been configured
- 20 BGP (Border Gateway Protocol)
- 90 EIGRP
- 100 - IGRP
- 110 - OSPF (Open Shortest Path First)
- 115 - IS-IS (Intermediate-System to Intermediate-System)
- 120 - RIP (Routing Information Protocol), uses hops as metric
OSFP routing; uses hello packets for communication, but it only sends the packets once it has a partnership with a router (partnership is only achieved when timer, subnet maks, security to access the area, etc, are all checked) Routers running OSFP have a "timer" to, let's say 30 seconds; timers between routers must match (otherwise they won't form a relationship) an if a router does not hear from another router within the timer span, it deletes its routes from its table. Areas of a OSFP domain represent an area of summarisation. OSPF uses cOst as a metric (remember Ospf for cOst)
The route-map ;this command is used to enable policy routing or conditions for router redistribution from one protocol to another
Routers support 3 types of packet-forwarding mechanisms: Process switching (the oldest, where every packet is treated in full), Fast switching (where a cache is created to improve speed) and Cisco Express Forwarding (where the changed in the cache are change-trigerred -changes on the network- and not packet-triggered, being therefore this method quicker and more proactive)
Routes that are directly connected to an interface (C) are removed from the routing table when the interface has failed or is administratively down. Note that directly connected routes overrride the Static routes that you may have configure ini a router.
The router changes the source and destination MAC addresses, while source and destination IP addresses remain the same. Remember that a switch does not change the frame in any way, it simply forward it to the appropriate port according to its MAC address table.
Frames sent to the default gateway have the local host source MAC address and the default gateway destination MAC address
To enable routing on a router do as follows:
- #conf t ;enter global configuration mode
- (config)#router rip ;enter router configuration mode for the rip protocol
- (config-router)#network 192.168.15.0 ;
The RIP network command tells RIP what network to advertise, for example the command (config)#network 10.0.0.0 will advertise all network starting with 10.x/24. IN ADDITION, the use of that command will also implies that these networks that have just been advertised, will be advertised too
ip classless ;instruct the router to use its default IP ROUTE to forward packets for unknown networks
(config-router)#no auto-summary
To block subnets from seeing one another: access-list 110 deny ip 10.10.10.0 0.0.0.255 10.10.20.0 0.0.0.255
20. Hot Standby Router Protocol (HSRP)
First Host Redundancy Protocol (FHRP) is the name of a family of protocols that add redundancy to routing. There are 3 FHRP protocols, being HSRP the one covered in the Cisco exam
| Name | Origin | Redundancy Approach | Load Balancing |
| HSRP - Hot Standby Router Protocol | Cisco | Active / Standby | Per subnet |
| VRRP - Virtual Router Redundancy Protocol | RFC 5798 | Active / Standby | Per subnet |
| GLBP - Gateway Load Balancing Protocol | Cisco | Active / Active | per host |
HSRP works by having a virtual IP address in the same range known by the participating routers/layer 3 devices, with a virtual MAC address referenced as VMAC1; the clients use that virtual IP as their default gateway. The participating routers send HSRP messages to one another to negotiate and decide which one will be the active router for the virtual IP address, while the other routers will be the hot-standby ones, waiting to take over the virtual IP in the event the active router fails. You can implement load-balancing in HSRP by having 2 x virtual IPs configured on the routers, each one serving a different subnet and being in an active/passive reciprocity.
1.(config-if)#standby 1 ip 10.10.10.1
Above joins the int of the router to HSRP group 1, telling to use virtual IP 10.10.10.1 for routing
2.(config-if)#standby 1 priority 110
Above tells the router to be at priority 110 in group 1, the highest priority wins the election in the event they boot up at the same time
3.(config-if)#standby 1 name HSRP_for_vlan_11
Above names the HSRP group 1 with a meanful name
#show standby brief ;gives you info where you can verify the active (local) router
#show standby ;gives more info than 'brief', showing counters and timers
By default preemption is disabled, but when you enable it on an interface with the command standby group-id preempt, you're telling the router to actively take over the "active" role if its priority is the highest
HSRP versions
There are two version in the HSRP protocol that are selected with the command standby version 1 or 2 ;versions must be the same for routers to negotiate properly, this is because the versions use different IPv4 headers formats. These are the differences in their features:
| HSRP v1 (uses UDP 1985) | HSRP v2 (uses UDP 1985) |
|
|
Troubleshooting; you'll get duplicated IP addresses (as well as all routers trying to be active) if the HSRP versions or groups mismatch
21. SNMP (Small Network Management Protocol) and Syslog
SNMP is an application layer protocol first published in 1988 RFC1065, where the SNMP Management Station (NMS) receive messages from the SNMP agent. Each agent keeps a database of variables that make parameters, status and counters for the device, this db is called Management Information Base (MIB). Cisco Prime is the Cisco product for SNMP. The agent send Traps and Inform messages which have kind of the same purpose but differ in the protocol mechanisms (both are sent through UDP, and while Traps are not reliable, Informs messages must be acknowledge by the receiver, otherwise the Inform message will time out and will be send again).
MIB defines each variable as an object ID (OID) which come in the format 1.3.6.1.4.1.9.9. etc, that's why is better to get a NMS to interpret those variables. To secure SNMP traffic, use IPv4 or IPv6 ACLs to permit packet from the source IP address to the NMS IP address.
- SNMPv1 and v2c uses clear-text passwords called communities, that can be read-only (RO get messages) or read-write (RW set messages)
- SNMPv3 does not use communities and provides message integrity, authentication and encryption
We use the snmp-server command to enable SNMP in the IOS as a whole, to disable it you first have to remove all the SNMP configuration with the no command, then turn off the agent
1.(config)#snmp-server community TEST RO ipv6 TEST_ACL ;enable snmp and filter "incoming" traffic with that ACL
2.(config)#snmp-server location LOCATION_TEST ;this command is optional
3.(config)#snmp-server contact CONTACT_TEST ;this command is optional
#show snmp community ;check that is active and working
#show snmp location
#show snmp host
#show snmp contact ;you can also use the "show snmp" command on its own to see the counters
To specifically send informs or traps to determine hosts, use these commands: snmp-server host 10.10.10.1 informs version 2c test1 OR snmp-server host 10.10.10.2 traps version 2c test2. In SNMPv3 the command snmp-server community is not used, instead it is used snmp-server group and snmp-server user for authentication, where each user must be a member of a group
1.(config)#snmp-server group TEST_GROUP v3 auth write access TEST_ACL OR v1default; where "v1default" is default MIB, allow write but without ACLs
2.(config)#snmp-sever user TEST_USER TEST_GROUP v3 auth md5 TEST_PASSWORD
the authentication hash could be MD5 or SHA, while encryption could be DES, 3DES or AES
Note that the TEST_GROUP name and the authentication method in used (noauth,auth,priv) need to match in both statements
These are the authentication methods use in SNMPv3 (note that all of them perform message integrity):
- noauth (noAuthNoPriv); authentication is provided but by username only (no password), does not encrypt either
- auth (authNoPriv) ;does authenticate but not encryption
- priv (priv) ;yes for authentication and encryption
To verify SNMPv3 you can use show snmp user, show snmp group as well as the almighty show run
To use Syslog in a Cisco switch, use the command logging host 192.168.0.130 or whichever the IP of the Syslog server. The use the logging trap (0,1,2,3, etc... depending of you choice below):
- 0 = Emergency (system is unusable)
- 1 = Alert
- 2 = Critical
- 3 = Error
- 4 = Warning
- 5 = Notification (normal by significant condition)
- 6 = Informational
- 7 = Debugging
The "conditions" are all accumulative, therefore if you chose to log trap 3, the conditions of Error (your choice) plus Critical, Alert and Emergency will also be logged.
#terminal monitor ;display in the VTY sessions the messages that may appear on the console
22. IP Service Level Agreements
Service Level Agreements (SLA) are contracts or agreements between two parties with one party supplying services to the other. Cisco provides a feature called IP Service Level Agreement (IP SLA) that measure the performance and availability for these agreements, to determine if the SLA is met over some period of time. IP SLA Operations (also known as IP SLA probe) are messages that mimic certain traffic, like RTP-base, VoIP operation, QoS treatment, etc; these IP SLA Operations are sent from the IP SLA Source (the source router) to the IP SLA Responder
(config)#ip sla 1
icmp-echo 10.10.10.1 source-ip 10.10.10.5
frequency 60 ;sends the icmp every 60 seconds, which is the default
threshold, history and other parameters
(config)#ip sla schedule 1 life forever start-time now
To troubleshoot IP SLA you can use show ip sla summary, show ip sla statistics 1, show ip sla history 1
23. Switched Port Analyzer - SPAN
SPAN is a tool that enables switches to make copies of Ethernet frames flowing through a switch and send them to a specific port for analysis (wireshark), troubleshooting and intrusion prevention systems (IPS). SPAN can also be configured to monitor a specific VLAN, regardless of how many ports are connected to that VLAN. Types of SPAN are:
- Local SPAN ;only one destination port can be use, but multiple source ports (including port-channels) can be selected in one session
- RSPAN ;Remote SPAN sends the traffic to another switch, and from there is forwarded to its destination
- ERSPAN :Encapsulated Remote SPAN, sends the traffic in a GRE tunnel to a layer 3 device, and then it is forwarded to its destination
1.(config)#monitor session 1 interface g1/0/1 - 2 rx ;monitor ports 1 to 2 only for received traffic you can use "tx" for transmit or "both"
2.(config)#monitor session 1 destination int g0/24 ;sends the monitor traffic to port 24
You can also do:
1.(config)#monitor session 2 source vlan 11
2.(config)#monitor session 2 destination int g0/23
To see if it all works use show monitor session all or show monitor detail. Take care not to overload the SPAN destination device
Cloud Computing provides self-service, meaning a script needs to be run if somebody if requesting a VM from a datacenter (datacenter normally follow the traditional top-of-rack (ToR) and end-of-row (EoR) physical switch topology). Cisco has a product called Cisco Intercloud Fabric that mitigates some of the challenges from moving workloads from a cloud provider to another. Cloud computing offer the following services:
- IaaS (Infrastructure as a Service) ;the processing power is provided to you, and you install the OS and Apps you like, AWS is an example
- SaaS (Software as a Service) ;the user picks the application only, most online e-mail is consider to fall under this category
- PaaS (Platform as a Service) ;this is a development platform, similar to IaaS but offering more developing tools, example are Google App Engine, Eclipse integrated development environment (http://www.eclipse.org) and Jenkins -java application- continuous integration and automation (https://jenkins.io)
Virtual Network Function (VNF) is a networking function implemented by the cloud provider for the customer as a VM that is managed by the customer
25. SDN - Software Defined Networking
Also known as Network Programmability, is a term that refers to how networks can change more easily to adapt to the ever-changing environments of virtual machines. Traditionally, everything that networking devices do can be organised in these 3 planes:
- Data Plane ;also called forwarding plane, deal with receiving, processing and forwarding data, for example encapsulation, de-encapsulation, add/remove of trunking header, tags, layer 3 routing, encryption, NAT, ACLs, port security and all tools that process packets and/or frames
- Control Plane ;refers to any action upon de data, and sits above the data plane. example are all routing protocols, IPv4 ARP, IPv6 NDP, STP, switch MAC learning and other tables to facilitate the forwarding of the data like routing tables. This is also called Distributed Control Plane, as their tools (routing protocol, etc) are distributed among many devices#s
- Management Plane ;include protocols that allow the engineer to manage the tools in the Control Plane, examples are telnet and ssh.
IOS runs in the CPU and uses RAM (the IOS control most of Control and Management planes); however, the Data plane and part of the Control plane (the one associated with MAC learning) reside on the ASIC chip (Application-Specific Integrated Circuit) which uses a special memory called TCAM (Ternary Content-Addressable Memory) to store the required tables for a faster table looup
With the implementation of SND, the Distributed Control Plane becomes a SDN Controller, which directly program the Data Plane on each device
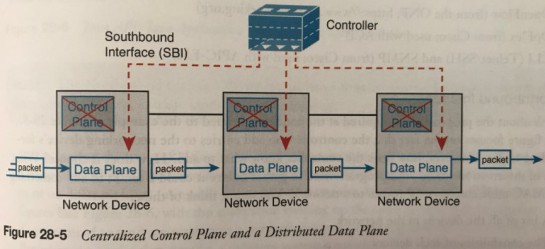
The Southbound Interface (SBI) is the way by which the controller communicates with the device, this SBI is normally an API, some examples are CLI (telnet, ssh), OpFlex (from Cisco) and OpenFlow
The Northbound Interface (NBI) is an API inside the controller that allows communication with programs and other APIs.
- 1.1 ;instruct the router to use the next hop IP (192.168.1.1, which is the IP of another connected router) in order to reach the network 192.168.3.0
- (config)#ip route 172.16.3.0 255.255.255.0 serial 0/0/0 ;instruct the router to use its interface serial 0/0/0 in order to reach the network 172.16.3.0
- #ping 192.168.0.1 source 192.168.1.1 ;this command instruct the router to ping to the address 192.168.0.1 but using the interface connected to 192.168.1.1, nice command to know for troubleshooting
- (config)# router ospf 23 ;configures the router to use ospf, with the process id of 23, this process id is entirely your choice
- #show ip arp ;displays the arp tables of the switch/router, matching IP address with MAC addresses
REST APIs (Representation State Transfer) are those that do not reside in the controller, and use HTTP GET to communicate with the controller API.
Now, let's have a look at 3 examples of Network Programmability and SDN:
1. Open SDN and OpenFlow
Open Networking Foundation (ONF) comes from https://www.opennetworking.org and it support switches, which function in the OpenFlow terminology is called switch abstraction. One of the most common controller of OpenFlow is the open source controller Linux-Foundation called OpenDaylight (https://www.opendaylight.org) that has many features and many SBIs. Cisco has its own SDN product called Cisco Open SDN Controller (OSC) which offer additional code and support
2. Cisco Application Centric Infrastructure
The goal of SDN is for software that can automate and change the network based on current conditions in the network. Cisco defined a different model for this approach of providing network programmability, a model that unlike OpenFlow is application centric, hence its name Cisco Application Centric Infrastructure (ACI). This model use a concept of endpoints (VMs that are organised in groups) and policies, and to make it all work Cisco uses a centralised controller called the Application Policy Infrastructure Controler (APIC), a GUI interface where the engineer can define which endpoints group need to access other endpoints groups, by the usage of policies. Once all this is define ACI will do the job using RESTful APIs and native APIs of communicating to the switches and program the correct flow as specified by the policy
3. Cisco APIC Enterprise Module
Even though APIC Enterprise Module (APIC-EM) uses the same acronym as APIC, it works significantly different; still developed by Cisco, it offer enterprise SDN using the same switches and routers already installed in networks. Visit https://developer.cisco.com to learn more, as well as http://www.sdnskills.com
London, 24 February 2019
References
- https://www.certskills.com/products/icnd2/icnd2simulator/
- https://www.learncisco.net/courses/icnd-2/wan-technologies/wan-connections-overview.html
Comments powered by CComment