Lab Setup for Microsoft Exam 70-410
This article shows you how to create and configure a technical lab setup for Microsoft Exam 70-410 - Installing and Configuring Windows Server 2012 , the exam will test you in the following topics of the Windows Server 2012 RTM and Windows Server R2 Operating Systems:
- Install and Configure servers (15-20%)
- Configure server roles and features (15-20%)
- Configure Hyper-V (15-20%)
- Deploy and configure core network services (15-20%)
- Install and administer Active Directory (15-20%)
- Create and manage Group Policies (15-20%)
This exam is compulsory towards your MCSA Windows Server 2012 qualification
- Stuff that is good to know about Windows Server 2012 R2
- Stuff that is good to know about Storage
- Stuff that is good to know about IPv6
- Stuff that is good to know about DNS
- Stuff that is good to know about Active Directory (AD)
- Stuff that is good to know about AD Groups and memberships
- Stuff that is good to know about Group Policy Objects
- Setup your Virtual environment - VMware vSphere
1. Stuff that is good to know about Windows Server 2012 R2
- The new Windows PowerShell 3.0 environment increases the number of available cmdlets from 230 to more than 2,430 (omg!)
- Server 2012 R2 Core Edition includes 12 of the 19 roles available on GUI mode, plus support for SQL Server 2012
- Roles not available on Core mode are: WDS, RDS, AD Federation Services, Application Server, Fax Server, Volume Activation Services and, of course, Network Policy and Access Services
- Disabling the Driver Signature; if an unsigned driver causes the server not to boot up, start on F8 > Advanced Boot Options > and select Disable Driver Signature Enforcement
- NIC Teaming increases performance by combining throughput of the adapters, providing fault tolerance. Note that only 2012 R2 has the feature to allow dynamic load balancing that continuously move traffic streams from NiC to NiC, the plain Windows Server 2012 does not have this feature. NIC Teaming in Windows Server 2012 R2 supports two modes:
- Switch Independent Mode; all nics are connected to different switches, providing alternative routes through the network
- active/active configuration; all nics are functional, and is one fails all traffic is shunted to the remaining ones
- active/passive configuration; a nic remains as standby to provide failover
- Switch Dependent Mode; all nics are connected to the same switch, providing a single interface with the combined bandwidth
- static teaming; generic mode to balance the traffic between the nics of the team
- link aggregation control protocol; this is defined on IEEE 803.3ax
- There are no big advantages of using Nic Teaming for large file transfer using TCP (like Hyper-V live migrations)
- Roles and Features can be installed on an offline VM by selecting its VHD hard drive
- The higher the value on "priority" the higher the priority of the printer; highest priority is therefore 99
- On Print Management, you can right-click a printer and select "Deploy with Group Policy...", how cool ha? Though for clients running XP, 2003 and earlier you need to configure the pushprinterconnection.exe with a script at user or machine logon for the printer on GPO to populate
2. Stuff that is good to know about Storage
- From Disk Management you can create a virtual hard drive with the format either VHD (supports up to 2TB size) or VHDX (supports up to 64TB but can only be read by 2012 OS systems)
- For hard drives to show up on a Storage Primordial Pool, they need to be bigger than 4TB? and obviously be unallocated
- For the "Always Offline" mode of "Allow Caching of files", you must set the Configure slow-link mode Group Policy setting on the client to a value of 1 millisecond
- Prior to Windows Server 2012, basic permission were known as standard permissions, and advance permissions were know as special permissions. NTFS systems has 6 basic permissions and 14 advance permissions
- ACL, Access Control List are the permissions, while ACE (Access Control Entries) are the security principals (user, group, etc) to which permissions are applied
- To create a mirrored space that could support up to two hard disk failures, you need at least five disks in a storage pool
3. Stuff that is good to know about IPv6
- There are only 3 possible methods by which administrators can assign IPv6 addresses:
- Manually; entering them o the ncpa.cpl adapter
- Stateless Autoconfiguration; the adapter will always assign itself a link-local IPv6 address (FE80::xx); they use the ND (Neighbors Discovery) protocol to detect possible duplications. If an IPv6 router is to be on the network, the link-local IPv6 address wi lbe use to genera a stateful configuration of the adapter
- DHCPv6; to assign unique-local or global-addresses you'll need either a router that advertise the proper network prefixes or a DHCPv6 server tthat can supply addresses with the correct prefixes
- To configure IPv6 packets into IPv4 packets (so that they can travel the Internet, which is mostly IPv4 anyway), you have to configure Tunelling. To manually configured a tunnel between to interface use the cmdlet: netsh interface ipv6 add v6v4tunnel "name" localAddress remoteAddress; where "name" is the name you want to give to the tunnel and the addresses should be in decimal notation format, e.g.: netsh interface ipv6 add v6v3tunnel "tunnel" 206.73.118.19 157.54.206.43
- These are the current transition technologies for expressing IPv4 address in the IPv6 format:
- 6to4; encapsulates IPv6 traffic into IPv4 packets
- ISATAP; Intra-Site-Automatic-Tunnel-Addressing-Protocol is an automatic tunnelling protocol that emulates an IPv6 link by using an IPv4 network. ISATAP does not support multicasting therefore it cannot locate routers using the ND (Neighbor Discovery) protocol, it uses instead ICMPv6
- Teredo; for Teredo tunnelling both endopoints of the tunnel must have registered IPv4 addresses. Teredo enable devices behind non-IPv6 routers to function as tunnel endpoints by encapsulating IPv6 packets with transport-layer UDP datagrams rather than network-layer IPv4 datagrams, as 6to4 does
- A nice table of how IPv6 addresses matches with their corresponding prefix:
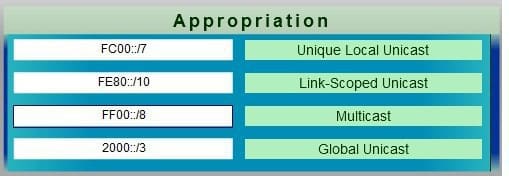
- Unique-Local Unicast (FC00::/7) are available for use in private networks and not routable in the global IPv6 Internet
- Link-local (Scoped) Unicast (Fe80::/10) are intended and valid only for communications within a single network link or one broadcast domain; in IPv4 link-local (scoped) addresses are defined as 169.254.0.0/16
- Multicast; (FF00::/8) are logical identifier for a group of hosts on a network segment. When a multicast occurs, all host on the network segment process the frames being sent
- Global Unicast (2000::/3); this allocation encompasses the entire IPv6 address range except the multicast range
4. Stuff that is good to know about DNS
- On all DNS servers create a AD-integrated zone called "confidential", then add some dummy A records in there, then created an application directory partition on each DNS server by running dnscmd . /createdirectorypartition DNSpartition.confidential and store the zone on that partition, see how it replicates to the other DNS
- Referral: the process by which one DNS server sends a name resolution request to another DNS server
- DNS server recognises two types of name resolution requests:
- Recursive query; the DNS server receiving the request takes full responsibility for resolving the name; if it has the information it replies immediately but if it doesn't it will send referral to other DNS servers until it finds the info needed
- Iterative query; the DNS server receiving the query response with the best information it possesses at the time
5. Stuff that is good to know about Active Directory (AD)
- Obviously, the 1st DC on a forest must be a Global Catalog (GC) server and cannot be a Read-Only Domain Controller (RODC); that is why both of these options are greyed out when installing the first AD on a forest.
- To install AD on a Server Core, install the ADDSDeployment module first; install-WindowsFeature -name -AD-Domain-Services -IncludeManagementTools
- A tip for installing AD on a core is to use a full GUI and then export the script file
- If domain controllers are located on different AD DS sites, no replication will occur until an administrator creates and configures the required site links
- When installing AD at a remote location, the first replication that occurs for the new DC will exchange a complete copy of the AD DS database, which may slow down the WAN link to a halt (subsequent replications will only contain objects that have changed since the last replication). To avoid this load on the WAN link, you can use the ntdsutil.exe with the command ifm (Install from Media), then once you install the AD at the remote location select the Install from Media checkbox and specify the path to the location of the folder. The sequence to install from media is:
- ntdsutil
- activate instance ntds
- ifm
- cretae full c:\ifm OR create rodc c:\ifm
- NOTE: you only use IFM to install a DC on an additional domain (but on the same domain!) and with the same Operating System, you cannot use IFM to install a FRDC or to copy the data from a 2008 R2 to a 2012 R2, or to export it to a different domain name, etc
- To install the first Windows Server 2012 DC onto a down level AD DS domain, you must supply credentials for a user member of the Enterprise Admins and Schema Admins groups, as well a member of the Domain Admins on the domain where the schema master host resides.
- To remove an DC from a domain, just uninstall the role (no need to use dcpromo); for a server core use the following; uninstall -ADDSDomainController -ForceRemoval -LocalAdminPassword "***" -Force
- If you have multiple domains with DCs located at multiple remote sites, it is recommended to place Global Catalogs (GCs) at each site, though the initial replication may generate lots of traffic, the saving in the long run should be significant; with a GC at each site you speed up the searches users perform on AD and keep them local.
- To confirm that a DC has been correctly registerd on DNS, open a cmd window and run:
dcdiag /test:registerdns /dnsdomain:myDomainName /v
6. Stuff that is good to know about AD Groups and memberships
- Obviously, do not use the Administrator account for daily donkey work, create a SystemAdmin for the purpose instead
- If you have enable it, rename the Guest account please. Also recommended to rename the Administrator account
- The most common methods to create multiple users and groups in AD are:
- dsadd.exe; to add a user using this command use the format: dsadd user "cn=Peter Blas,ou=Finance,=ou=microsoft,ou=com" -samid pblas ; notice that the quotation marks comprises the whole distinuished name
- Windows PowerShell, in particular the maintenance tool. the New-ADUser cmdlet can be used to create new users as well as the Import-CSV cmdlet
- CSVDE.exe, this utility import information from a comma-separated value (csv) file; csvde.exe -i -f filename.csv, where the -i switch indicates the operation will import data while the -f switch specify the file containing that data
- LDIFDE.exe; Light Data Interchange Format Directory Exchagne, works like CSVDE but is more flexible as you can add,delete or modify objects including the schema, helping you modify the objects once they have been imported
- To join a computer to a domain you can use the netdom join command
- To join a computer to a domain while offline, use the djoin command; the way it works is that you need to run it first on a computer with access to a DC (this is to safe the comptuer account metadata on a file), and then on the offiline comptuer to be join, like this:
- djoin /provision /domain microsoft.com /machine computer1 /savefile File1.txt
- djoin /request0DJ /loadfile File1.txt /windowspath %SystemRoot% /localos
- Any user who is successfully authenticated to AD can add up to 10 computer objects to the domain
- There are two types of groups on AD:
- Security Groups; use to assign permission to resources
- Distribution Groups; use for non-security related functions, AD applications (like for example MS Exchange) use global groups to send messages to multiple users
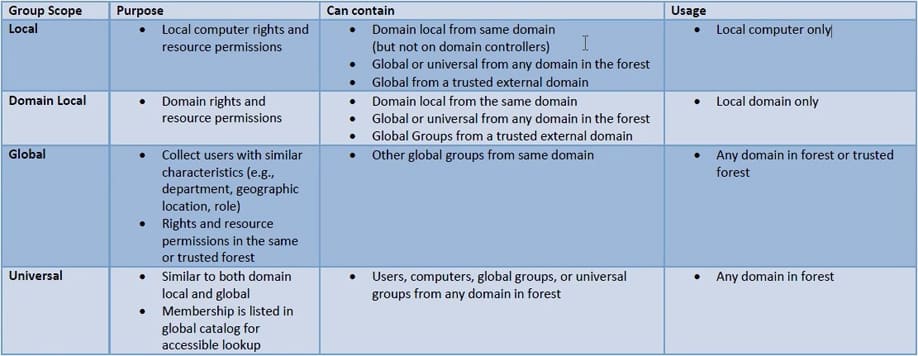
- Group Scope determine what object the group can contain, the groups scopes of AD are local groups, global groups and universal groups.
- AGUDLP = Accounts > Global groups > Universal groups > Domain Local groups > who get the permissions
- Using GPO, when you add a group to the Restricted Group configuration (Computer Configuration > Policies > Windows Settings > Security Settings > Restricted Group folder), nobody can add/remove members from that group
- The DSMOD.exe allow you to modify the properties of existing groups
- The following applies when converting groups:
| - |
To Domain Local Security |
To Domain Local Distribution |
To Global Security |
To Global Distribution |
To Universal Security |
To Universal Distribution |
| From Domain Local Security | - | Not permitted | Not permitted | Permitted only when the domain local groups does not have other domain local groups as members | ||
| From Domain Local Distribution | - | - | Not permitted | Not permitted | ||
| From Global Security | Not permitted | Not permitted | - | Permitted only when the global group is NOT a member of another global group | ||
| From Global Distribution | Not permitted | Not permitted | - | |||
| From Universal Security | Okay | Okay | Permitted only when the Universal group does not have other universal groups as members | - | ||
| From Universal Distribution | Not permitted | Not permitted | Possible, but Global Security can only contain stuff from its own domain | - |
The key things to remember is that:
- Local Groups can contain users or groups from any domain (that's why they apply the permissions)
- Global Security can only contain objects from its own domain
- Universal Security can contain anything within the forest, but for best practices is best to include only groups into Universal groups, because its memberships are replicated to all Global Catalog servers in the forest, too many changes will increase replication
More of the above here: 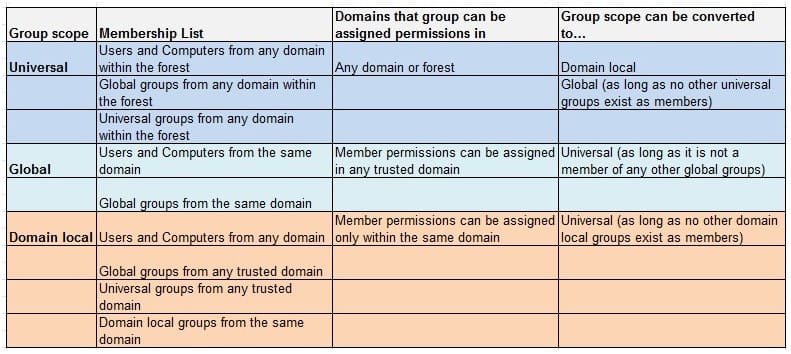
7. Stuff that is good to know about Group Policy Objects (GPO)
- In Windows 2008, Vista, Microsoft replaced the token-based administrative template (ADM) file with an xml-based file format (ADMX). This addressed the "sysvol bloat" problem, where hundreds of megabytes of ADM files (each adm file could be about 4MB) had to be replicated to all DCs. Now, with ADMX format, the file could be stored on a folder called "Central Store" where all DCs will have access, thus avoiding the payload of replication.
- To create a Central Store folder, copy the PolicyDefinitions folder to the same location as the Group Plicy templates, that is, from C:\Windows\PolicyDefinitions to %SystemRoot%\SYSVOL\sysvol\DomainName\Policies
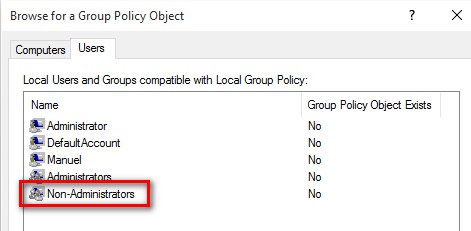
- Windows applies the local GPOs on the following order:
- Local Group Policy; consist of both computer and user settings, and applies to everyone
- Administrative and non-administrative Group Policy; these are in fact 2 x GPOs, one that applies to the local Administrators and another for everybody else; these GPOs do not include computer settings
- User-Specific Group Policy; this GPO applies to local user accounts only; it does not contain computer configuration either
- To create the above GPOs open mmc and add the Group Policy Object, and at the time of configuring click on "Browse..." and on the next window select the "Users" tab
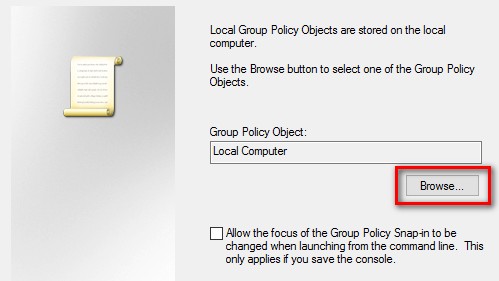
Domain Controllers of OS previous to Vista will not have/support the multiple local GPOs, and therefore won't have the users's tap
Using Security Templates (files with the extension .inf) you can deploy settings like audit policies, user rights assignments, security options, event log policies and restricted groups
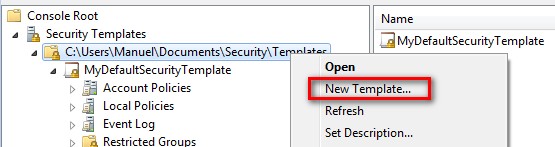
To create a Security Template, launch the mmc and add the Security Templates snap-in, then right-click on your entry to create a new template
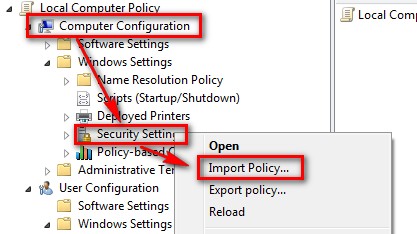
To import a Security Settings template on a GPO, edit the GPO and then right-click the Security Settings inside the Computer Configuration and choose to "Import Policy..."
Use the command scwcmd (Security Configuration Wizard) to import an .xml security policy file
8. Setup your Virtual environment - VMware vSphere
If during the Server 2008 R2 exams we were using Hyper-V, it is time now to move to the more powerful and resilience VMware vSphere, yeehaa!
Okay, using VMware Workstation, create this number of VMs:
| Name | IP Address | Role |
| FRDC | 10.10.10.71 (VMnet3) | Forest Root Domain Controller (2008 R2) Also runs DHCP from 10.10.10.150 to 10.10.10.170 |
| VCENTER55 | 10.10.10.52 (VMnet3) | vSphere vCenter 6.0 (Windows Server 2012 R2) |
| HOST1 |
10.10.10.21 (VMnet3) 10.10.10.31 (VMnet4) 10.10.10.41 (VMnet5) |
ESXi 6.0 |
| HOST2 |
10.10.10.22 (VMnet3) 10.10.10.32 (VMnet4) 10.10.10.42 (VMnet5) |
ESXi 6.0 |
| SAN1 | 10.10.10.201 (VMnet4) | FreeNAS |
| SAN2 | 10.10.10.202 (VMnet5) | FreeNAS |
| SAN3 | 10.10.10.203 | FreeNAS (with a 2TB hard drive) |
So, based on the above, for your own testing VMs just use the static IPs from number 80s to 90s
PowerShell commands - cmdlets
Okay, we're back to our beginning, the lovely black window of MS-DOS, love it that Microsoft has decided to empower Powershell finally on all its Server OSs. Let's have a look at the most common PowerShell cmdlets that we may use for this exam and beyond.
Uninstall-WindowsFeature Server-GUI-Shell -Remove ; removes the GUI from the Server (effectively becoming a Core Server) and also removes the WinSx folder (where all the OS modules are stored) enabling on demand installation
Uninstall-WindowsFeature Server-Gui-Mgmt-Infra,Server-Gui-Shell -Restart ; convert the full GUI installation to Server Core
Okay, to convert a Core server to full gui server, do as follows:
- Import-Module ServerManager
- Install-WindowsFeature Server-Gui-Mgmt-Infra, Server-Gui-Shell -Restart ; if you use the "remove" switch the binary files are removed from the server (a .wim source will be needed to install the gui back)
To remove features from a vhd drive: PS> uninstall-windowsfeature -name gpmc -vhd "C:\drives\myvh.vhdx" -remove; where "gpmc" is on this example the name of the feature
To use Minimal Server Interface
- For a full GUI, remove the feature User Interface and Infrastructure > "Server Graphical Shell"
- For a Core, run: PS> uninstall-windowsfeature Server-gui-shell
netdom renamecomputer %ComputerName% /NewName:VM01 ;renames the server name to whichever names it has to VM01
netdom join %ComputerName% /domain:
set-NetFirewallRule -DisplayGroup "Remote Desktop" -Enabled True ; enable Remote Access.
c:\Windows\System32> cscript scregedit.wsf /AR 0 ; sets to zero (meaning it is enabled) the fDenyTSConnections entry on the register, effectively enabling Remote Access; use the /v switch to display the status (1 = disabled, 0 = enabled)
To manage and configure WinRM (Windows Remote Management) you can use Configure -SMRemoting.exe -Get (display status) -Enable (enables WinRM) -Disable (disables WinRM)
To remotely configure a Windows Firewall on another system, you must enable the following inbound Windows Firewall rules on the remote server you want to manage:
- COM+ Network Access (DCOM-In)
- Remote Event Log Management (NP-In)
- Remote Event Log Management (RPC)
- Remote Event Log Management (RPC-EPMAP)
- Enable the Windows Remote Management (HTTP-In)
To configure the above firewall rules on PowerShell use the command Set -NetFirewallRule - name "rule-name" -enabled True; to obtain the name of the rules use the cmdlet Get-NetFirewallRule
To add WinRM support to servers running 2008 R2 or earlier you must install on them .Net Framework 4.0 and Windows Management Framework 3.0
To run PowerShell ISE (Integrated Scripting Environment) run powershell_ise
Storage Pool
To obtain the designation for the hard drives use Get-StorageSubsystem and Get-PhysicalDisk cmdlets, and then use New-StoragePool -FriendlyName "myname" -StorageSubsystemFriendlyName "subsystem name" -PhysicalDisks "disk names" to create a new storage pool
To enable to run MMC Disk Management on a Remote Server, run: enable-netFirewallRule - DisplayGroup "Remote Volume Management"
You have roles and features, but then again, in PowerShell, everything is a feature! (install-windowsfeature xxx)
Additional tips
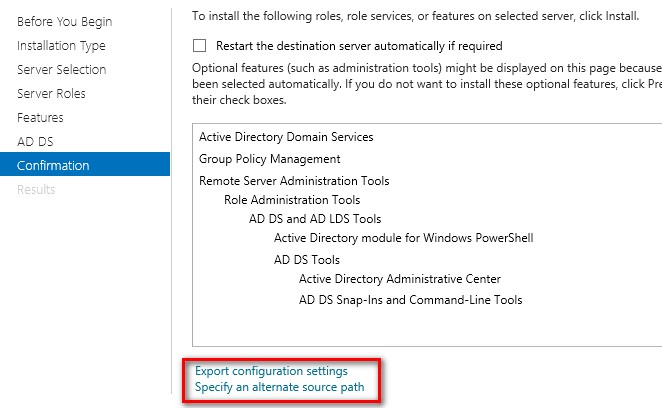
1.-When adding a new role/feature, you got the option to export the configuration setting to a xml file (that can be used later with PowerShell), as well as the facility to specify a different location for the SxS folder in case it has been remved from that particular server
Great stuff from CBT Nuggets: this awesome table describes on one show the golden rule AGDLP (Accounts goes into Global group that goes into Domain Local groups who gets the Permissions)
To remote manage a Server Core that is not part of a domain, first of all run sconfig on it and "Enable Remote Management", then from the workstation run this command to add the credentials to logon to the server on the workstation: cmdkey /add: SERVER1 /user:Administrator /pass:Change_Me
The Security Levels of the Software Restrictions Policies (Computer/User Configuration > Windows Settings > Software Restriction Policies > Security Levels):
- Disallowed; prevent running all applications expect those that are specifically allowed
- Basic Users; prevent running applications that require administrative rights
- Unrestricted; run all applications except those that are specifically excluded
Note that, when implementing multiple rules types, the system applies the rules in the following order of precedence, so when a conflict occurs, the one on the top prevails, and if two identification collide (two set of hash rules, for example), the most restrictive always wins:
- Hash rules
- Certificate rules
- Network zone rules
- Path rules
Using the "Designated File Types" you can specify what extensions are treated as executable, for example, removing the .msc extension will allow all .msc to run

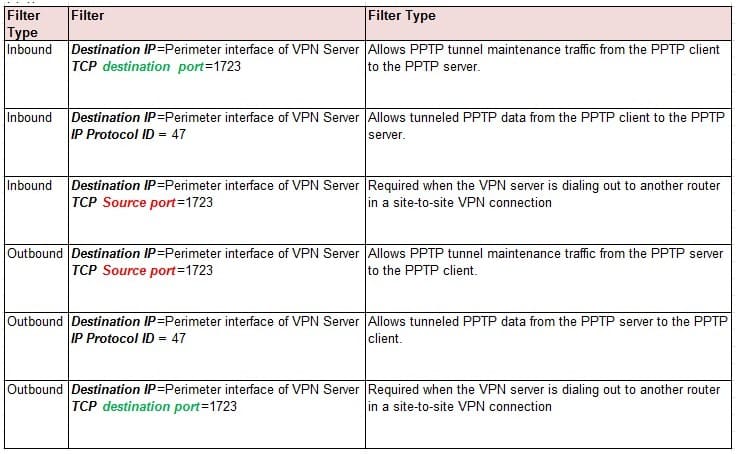
PPTP Ports that need to be open:
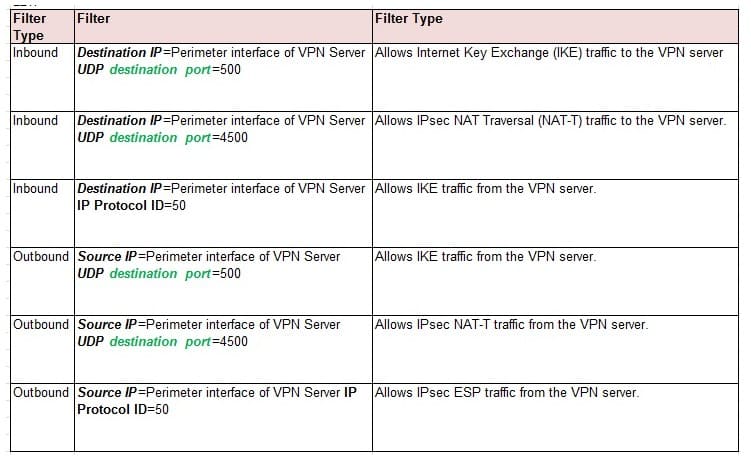
L2TP ports that need to be open:
Stuff that is good to know about AppLocker
For AppLocker to work the service "Application Identity" must be running, which manual is set to manual startup, so we have to change it and make it automatic
- The great advantage of AppLocker over Software Restrictions Policies is the ability to create rules automatically
Stuff that is good to know about Deploy and Migrating
To mount an image use: dism /mount-image /ImageFile:D:\Temp\image.wim; once the image is mounted use the /Get-Features to find out what features are available on the OS. This, for example, will enable the SMTP feature: dism /image:D:\Temp\image.wim /Enable-Feature /FeatureName:SMTP-Server /All ;After the feature is enable, unmount the image and use the /Commit command to apply the changes: dism /unmount-image:D:\Temp\image.wim /Commit
Stuff that is good to know about Windows Firewall
It works by applying any of these 3 criteria:
- IP Addresses: allowing or blocking specific computers or networks
- Protocol numbers; the protocol number specifies whether the packet contains TCP or UDP traffic
- Port numbers; port number specifies what kind of application is running on the computer
When you Turn On Network Discovery, you are effectively activating firewalls rules for ports 137,138, 1900, 2869,3702, 5355 and 5358
When you export a policy from the Windows Firewall with Advanced Security console, the format of the file is *.wfw (Windows FireWall)
When you import a policy using a *wfw file, the policy overrides everything on the local computer, but when the firewall policy is applied using a GPO, it merges with the existing local policy (of course, if there is conflict, the GPO always wins)
Hyper-V 2012 R2 + Server Core
These are the limitations of Windows Server 2012 R2 Hyper-V host system:
- the host can have up to 320 logical processors
- the host can support up to 2,048 virtual CPUs
- the host can support up to 4TB of physical memory
- One host can have as many as 1,024 active VMs, where each VM can have up to 64vCPUs and 1TB of vRAM
To create a VM using PowerShell, use this command:
New-VM -Name "MyNameVM" -MemoryStartupBytes 1GB -NewVHDSizeBytes 60GB
To enable resource metering for a particular VM use: Enable-VMResourceMetering -ComputerName "MyNameVM" ; To display the statistical report of the resource metering use: Measure-VM -VMname "MyNameVM"
To install File Explorer and Internet Explorer on a server core Windows SErver 2012 R2 server, use this command: Install-WidowsFeature Server-Gui-Shell -Restart
Generation 2 vs Generation 1:
- Generation 2 VMs support the ability to boot from a device attached to a SCSI controller, generation 1 do not
- Generation 2 supports only VHDX virtual drives, generation 1 support both (VHD and VHDX)
- A legacy network adapter (for PXE) is not available on a generation 2 network adapter
London, 29 December 2017
References and further reading
- Hyper-V cannot be installed. A hypervisor is already running; thanks to Scott Lowe for providing the solution to this problem http://www.virtualizationadmin.com/blogs/lowe/news/fix-hyper-v-cannot-be-installed-a-hypervisor-is-already-running-message-in-fusion-and-workstation-293.html
- RAID5 on Disk Management vs Storage Pool, which one to choose?; create a storage pool gives you more flexibility than creating the same thing on disk mangement, as Brien M. Posey clearly explains here: http://www.windowsnetworking.com/articles-tutorials/windows-server-2012/Getting-Used-Using-Windows-Storage-Spaces-Part1.html
- Windows Server 2012 Storage (pool) Virtualization Explained; awesome graphics from Yung Chou, well done! https://blogs.technet.microsoft.com/yungchou/2013/04/11/windows-server-2012-storage-virtualization-explained/
- VMware Performance Enhacing Tweaks; great tips from Art Kulaga to get the most of the VMs running on your VMware Workstation http://artykul8.com/2012/06/vmware-performance-enhancing/
- Windows 2012 R2 Internet Explorer Can't Be Opened Using Administrator Account; credits to Will Kruss for a nicely presented troubleshoot to this problem https://www.vpsblocks.com.au/support/Knowledgebase/Article/View/211/8/windows-2012-r2-internet-explorer-cant-be-opened-using-administrator-account
- Advanced Subnet Calculator; thanks to the guys/gals at Solarwinds for providing this... free! http://www.solarwinds.com/freetools/advanced-subnet-calculator.aspx
- Cannot connect to vCenter Single Sign-On server; if you are presented with this error when trying to logon to vCenter, upate your version of Java and restart the vSphere Web Client service on the vCenter server

Comments powered by CComment