How to audit user logon sessions in Active Directory using Event ID
This article explains you how to audit user logon sessions in Active Directory using Event ID that can be found in the Windows Operating System
The new settings can be found in Group Policy under Computer Configuration\Policies\Security Settings\Advanced Audit Policy Configuration, and the original audit settings can be found here: Security Settings\Local Policies\Audit Policy.If you have Active Directory installed on your network, you might experience the need to find out who has logon to what computer and when. In this guide we'll explore how to do this
First of all, a summary of the Event IDs that we need to look for:
| Event ID | Type | Description |
| 4624 | Success | A user successfully logged on to the Domain |
| 4625 | Failure | An account failed to log on to the Domain |
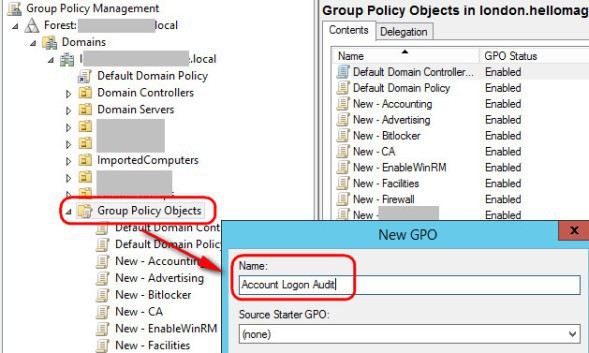
Create the GPO
Open Group Policy Management in your Forest Root Domain Controller (FRDC) and create a new GPO called "Account Logon Audit"
Edit the newly created policy, then visit Computer Configuration Policies >> Windows Settings >> Security Settings >> Local Policies >> Audit Policy >> Audit account logon events and define the policy setting as enabled for "success". Optionally, you can also enable the "failure" is you want to record when somebody enters a wrong password or username
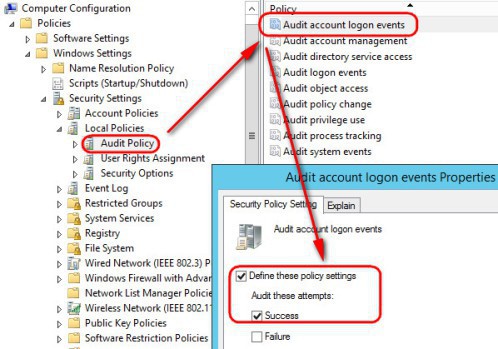
Once you have done that, visit .... Security Settings >> Local Policies >> Security Options and enable "Audit: Force audit policy subcategory setting" ; that will set the "SCENoApplyLegacyAuditPolicy" in the registry preventing basic audit policies from being applied

Edit the newly created policy, then visit Computer Configuration > Policies > Windows Settings > Security Settings > Local Policies > Security Options > Audit: Force audit policy subcategory setting, and set it as "Enabled". That will enable the advanced auditing policies for us

When using "Advanced Audit Policy Configuration Settings" you need to ensure these settings are not overwritten by basic audit policy settings. The following procedure shows how to prevent conflict by blocking or disabling of any basic audit policy setting, thus preventing from Basic (9 settings only) and Advanced Audit (53 settings in total) Policies from being mixed. The new settings can be found in Group Policy under Computer Configuration\Policies\Security Settings\Advanced Audit Policy Configuration, and the original audit settings can be found here: Security Settings\Local Policies\Audit Policy.
Finally, visit your OU and create a new group called "Group Account Logon", this is the group to which the GPO will be applied. Add into that group the computers and users that you want to log
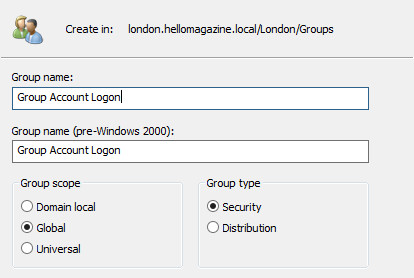
Add the Group Account to the Security Filtering of the GPO
Visit the client computer (after running gpupdate /force) in question and run the following to determine if the advanced policies have been applied
A test command that you can issue too is: auditpool /get /category:*
If you like this article about how to audit user logon sessions in Active Directory using Event ID, you might be interested in this other one too: https://www.nazaudy.com/setup-and-configure-a-public-key-infrastructure-pki
References
- https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventID=4624
- https://www.morgantechspace.com/2013/10/logon-and-logoff-events-in-active.html
- https://docs.microsoft.com/en-us/windows/security/threat-protection/auditing/basic-audit-logon-events
- https://www.netwrix.com/how_to_detect_who_deleted_user_accounts.html
- https://petri.com/enable-advanced-audit-policy-configuration-windows-server/
Comments powered by CComment